Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
IntelX Darknet Search
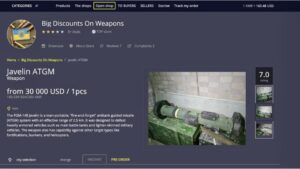
- The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more.
- The use of the dark web raises suspicion as it shows there is something you want to do privately.
- They’re tightening security and carefully screening anyone who wants to join.
- As such, they are normally under intense scrutiny from law enforcement and security professionals alike.
- Russian Market has consistently remained one of the most popular and valuable data stores on the dark web.
Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage. Like other marketplaces, it also requires registration for new users and accepts payments in Monero. Empire Market is a dark web shop that resembles the AlphaBay marketplace.
The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control.

In fact, some of the most profitable illegal digital products on the dark web are crypto accounts, online banking credentials, and e-wallets. It was quite popular for selling a wide range of products and services. It offers impressive features, including PGP-signed addresses, payment via Monera, sticky and featured listings, and auto shops. In 2017, the website went offline following a law enforcement action taken by the American, Canadian, and Thai authorities, but since August 2021, it’s been operational again. You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information.
Measures Against The Trade In Illegal Data
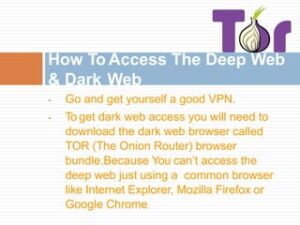
These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. Join millions of users who trust ForestVPN for privacy and unrestricted internet access. This approach is vastly more time-efficient and allows you to put your web monitoring on auto-pilot, reducing costs while simultaneously increasing efficacy.
Western drug flows in particular come from US-domiciled exchanges and trace flows from those to darknet markets. The entity “DNM Aggregator” that appears within each category refers to a service we’ve identified as being in control of multiple, disparate darknet markets. Throughout the history of the darknet market ecosystem, at different turns one marketplace has typically played the dominant role. The last several years’ examples include Silk Road, AlphaBay, Wall Street Market, and Hydra, most recently. Historically, as law enforcement closed each dominant marketplace, a new leader emerged. We can see this pattern on the chart below, which shows the level of market share controlled by the dominant market of each epoch.
Cross-reference Findings With Other Intelligence Sources
In April 2022, local authorities took down Hydra’s Germany-based servers and seized $25 million in Bitcoin. The investigation revealed that Hydra had more than 19,000 sellers and a total of 17 million customers during its two years of activity. As its contents are unindexed, it’s impossible to determine the Dark Web’s exact size. However, experts estimate it accounts for no more than 5% of the internet.
Stay Within Legal Boundaries
I grabbed mine from the official site a while back after dodging a sketchy mirror that tried to sneak in some junk software. It locks your messages so only the right person can read them—super handy when you’re dealing with sensitive stuff on the dark web. Markets like Incognito even nudge you to use it for extra peace of mind.
How To Keep Track Of Evolving Darknet Marketplaces
As I’ve previously said, it’s a good idea to keep your interactions with the dark web to a minimum, unless you can absolutely trust the people you’re dealing with. You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. The FBI Cleveland Field Office is investigating the case with assistance from the DEA and IRS-CI in Chicago.

Primary Risks For Users Of Darknet Marketplaces
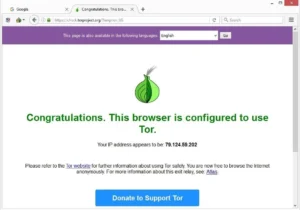
Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites. The majority of the users on the dark web use the Tor (The Onion Router) browser. A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users.
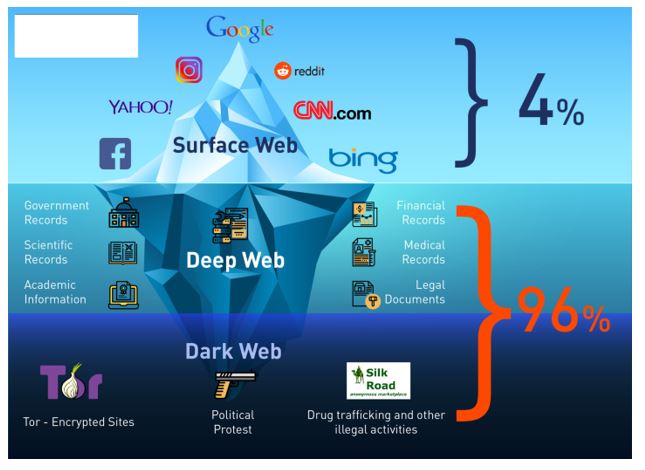
Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions. Users favor marketplaces with straightforward navigation, efficient search functions, and clear product categorizations. The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience.
- To help Genesis Market victims and prevent future crimes, the Dutch Police created a Check your hack tool that lets victims see if their credentials were sold or for sale on Genesis Market.
- Moreover, the company also uses HTTPS and SSL encryption on the Onion site for extra protection.
- Instead of “.com” or “.org”, dark web addresses can be distinguished by the top-level domain, “.onion“.
- If you are planning to make a purchase on the dark web, you should really take the time to learn how PGP encryption works.
- Future markets will likely adopt more decentralized architectures, but persistent flaws in human operational security (OPSEC) and software misconfigurations will remain their Achilles’ heel.

And since fewer people were investing in cryptocurrency, there were fewer new accounts to hack. As such, you should exercise caution when accessing any unofficial dark websites. The dark web allows people to access and share all sorts of illegal and explicit material without judgment or censorship. Tor is a network of volunteer relays through which the user’s internet connection is routed. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information.
WiFi Hacking Software

Some dark web listings claim to offer services like hacking-for-hire or even hitmen. These listings often include detailed descriptions, user reviews, and even shipping guarantees. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud.