At the time, it had over 600,000 users, 17,000 listings, and approximately €250 million in transactions. Authorities seized €7.8 million and arrested operators in Germany, Spain, Sweden, Romania, the Netherlands, and the US Europol leads takedown of Archetyp. Russian Market has operated since 2019, specialising in stolen credentials, stealer logs, and remote desktop access. Threat reports consistently rank it among the top ten darknet sites Top 10 Dark Web Markets. As UniCC retires, focus will now be on who emerges as the main successor. The carding market overall recently surpassed more than $1.4 billion in sales with Bitcoin alone.
Exclusive Monero usage signals a heightened prioritisation of anonymity. For police, who would prefer criminals to face justice, this kind of exit causes mixed feelings. Some fullz even include photos or scans of identification cards, such as a passport or driver’s license.
Detecting Fraudulent Activity On Your Accounts
By monitoring the dark web, you can quickly identify when your cards are compromised through partner organizations or merchants. Network segmentation is absolutely critical for businesses handling card data. Security teams monitor for telltale signs of card data exfiltration. Financial institutions tighten their security measures to prevent fraud but that also prevents legitimate transactions as a result.

Protecting Yourself From Credit Card Fraud On The Dark Web
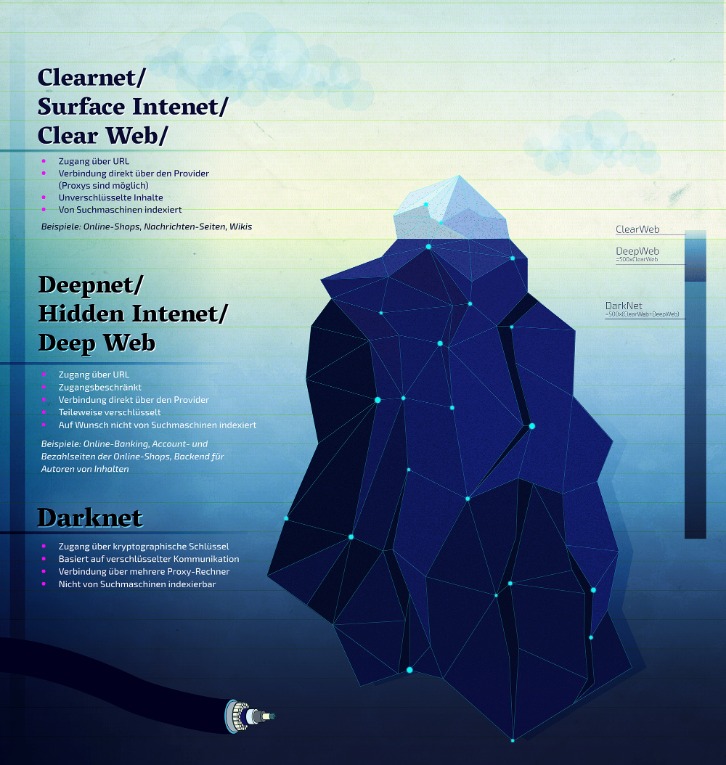
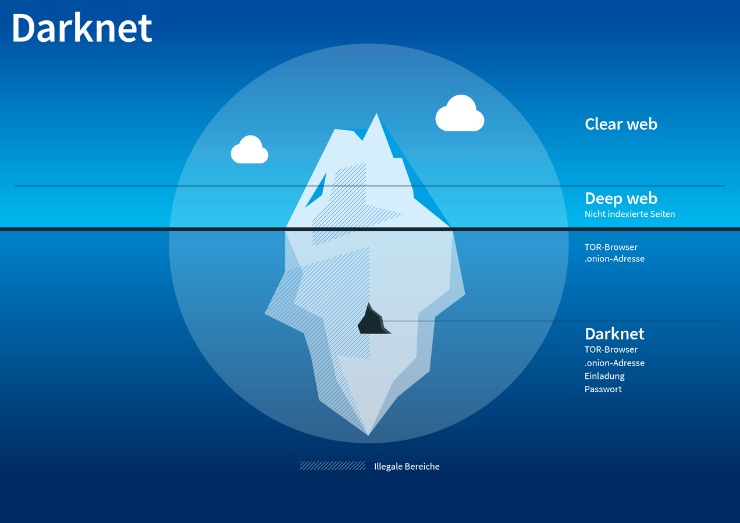
The Dark Web is a hidden part of the internet that can only be accessed through specialized software. It operates beyond the reach of normal search engines and is known for its anonymity. Criminals take advantage of this anonymity to carry out illegal activities, including the buying and selling of stolen credit card information. On the Dark Web, hackers and fraudsters can find a wide array of resources to exploit credit card data, such as sale platforms and forums. The sale of credit card data on darknet marketplaces is a significant threat to individuals and businesses. It is a lucrative business for criminals and a potential nightmare for victims.
How To Protect Yourself From Identity Theft
These generated numbers link to your real card but can be limited by merchant, amount, or time. Early detection enables your security team to prevent a transaction, minimizing the risk of a chargeback. I can’t stress this enough, your point-of-sale systems should never share a network with general-purpose computers or IoT devices. Instead of storing actual card numbers, each card should be converted into a unique token. We’re not just looking for individual red flags, we’re building comprehensive risk profiles based on dozens of different indicators.
Range Of Available Products
B1ack’s Stash’s sudden rise in popularity has been met with mixed reactions from dark web users. Most comments range from negative to neutral, while very few users gave clearly positive endorsements based on their site experience. The abundance of purchasable data has led to a bulk sales mentality for dark web customers.
Financial institutions can proactively strengthen their defences by integrating intelligence derived from FraudAction. This not only protects against financial losses but also reinforces customer trust. This victory against cybercrime dealt a severe blow to the criminal underground, disrupting operations on one of the most prolific dark web platforms. The threat actor’s marketing strategy involves leaking a large number of credit cards to attract potential clients from hacking and cybercrime forums. This move is likely to increase the platform’s popularity and draw in new customers. Card Shops typically host the trade of credit cards and other stolen financial information, making it easy for cybercriminals to find what they’re looking for.

Is Claude Safe And Secure In 2025?
On top of all that, they could make purchases or request money from contacts listed in the PayPal account. Hijacking a PayPal account requires a different approach than stealing a credit card number. Instead of card numbers and CVVs, criminals steal usernames and passwords that they’ve gathered either through phishing or malware. They can then sell the account credentials to a buyer who can log in and drains the funds, or the vendor can transfer the requested amount of money from the victim’s account to the buyer’s account. Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions. Stolen credit card details can be categorized into different types, making it easier for cybercriminals to exploit them.
- While these guidelines may appear complex and bothersome initially, they will become second nature once you become accustomed to them.
- Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data.
- Purchases in the darknet markets are typically made using virtual currencies like Bitcoin.
- These platforms have been competing for dominance in the Russian-language darknet market space.
- Ulbricht’s hefty prison sentence did not appear to have the intended deterrent effect.
Future Trends And Predictions For Dark-Web Marketplaces Beyond 2025
Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. As with our previous reports, we gather data by scanning Dark Web marketplaces, forums, and websites.

They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. As mentioned earlier, launching a cyberattack doesn’t require any hacking skills. Even people with zero technical knowledge can buy phishing kits, ransomware, or stolen logins. If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets.
The consequences of credit card fraud are not limited to financial loss, as it can also damage the reputation of banks and businesses. In this section, we will explore the global impact of credit card fraud on banks, businesses, and consumers. The use of darknet markets for the illicit credit card trade has far-reaching consequences for individuals, businesses, and the economy as a whole. Victims of credit card fraud can suffer significant financial losses, and businesses can face reputational damage.
Top 10 Dark Web Markets
Barry Elad is a tech enthusiast who loves diving deep into various technology topics. He gathers important statistics and facts to help others understand the tech world better. With a keen interest in software, Barry writes about its benefits and how it can improve our daily lives. In his spare time, he enjoys experimenting with healthy recipes, practicing yoga, meditating, or taking nature walks with his child. Barry’s goal is to make complex tech information easy and accessible for everyone. The surface web contains information that is easily available on the internet, and we are able to access it by surfing the internet, for example, YouTube, Wikipedia, Facebook, Google, blogs, and much more.
BriansClub remains a long-standing credit card data shop since at least 2014. Despite a 2019 breach that exposed over 26 million credit cards, it continues to operate, indicating sustained trust in its data pipelines. Implementing a 3-D Secure ACS solution, like Outseer 3-D Secure, fortifies the fraud prevention strategy.
- The software was developed in the mid-1990s to protect U.S. intelligence communications online and is used in conjunction with virtual private networks (VPNs).
- It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
- Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops.
- Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions.
- Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
It consists of websites specifically designed to be anonymous and only accessible through special software like Tor. These websites use complex addresses ending in “.onion” instead of familiar “.com” endings. The surface you see with search engines like Google is the “clearnet,” but a much larger portion lurks beneath the water – the deep web. This deep web encompasses everything not indexed by search engines, including private databases, paywalled content, and, yes, the dark web.
Established in 2020, Awazon Market has quickly become one of the most famous darknet marketplaces. The market claims to provide secure and anonymous commerce services. You can find a lot of goods and services packed with stealth high-level encryption, no JavaScript, and anti-DDoS protection. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts.