But there are also many illegal activities that happen on the dark web. And just like in real life, using the dark web for criminal purposes is never legal. The Hidden Wiki is a surface website offering a collection of dark web links. Before visiting any dark websites, get comprehensive cybersecurity software to help protect yourself from threats you may encounter.
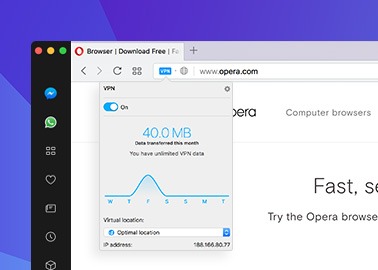
VPN Over Tor
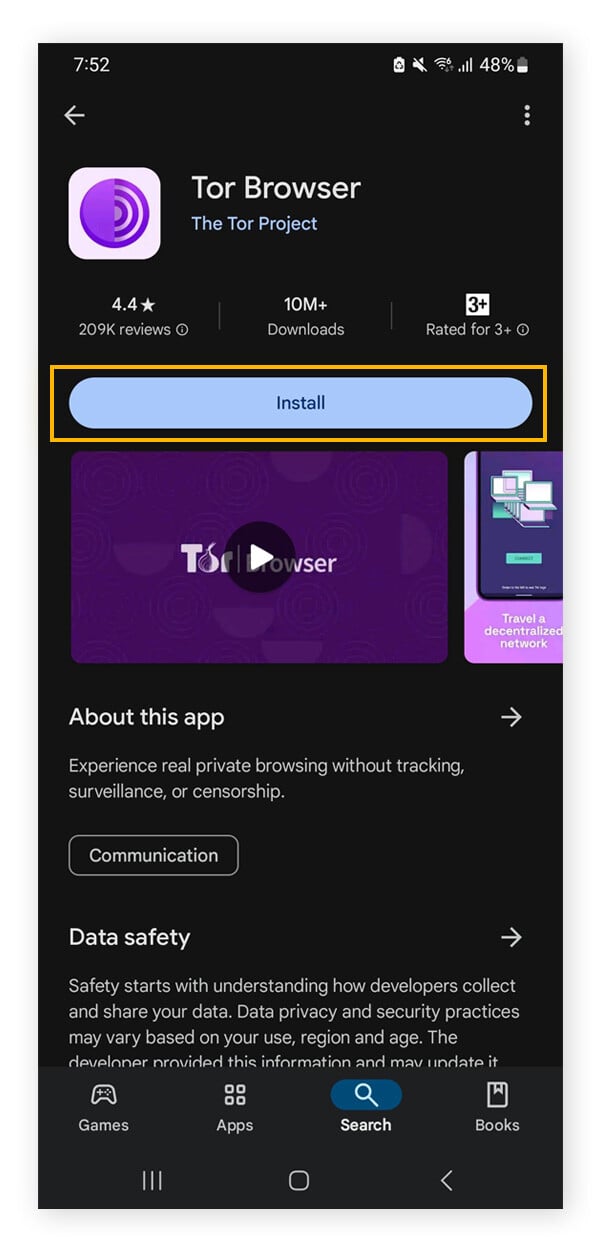
You can download the Tor browser from the official website, Torproject.org. There is no official Tor version for iOS because Apple requires all iOS browsers to use WebKit, which affects Tor’s privacy features. The Onion Router (Tor) was developed in the 1990s by researchers and computer scientists at the United States Naval Research Laboratory. It derives its name from the encryption system, which is structured like the layers of an onion.
The Tor Browser – What Is It?
That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t. The Tor browser stands as the venerable luminary of darknet browsers, leveraging onion routing and encryption for unparalleled anonymity.
Users must exercise caution when navigating unknown websites to prevent compromising their personal information or devices. Probably not, which is why many security-conscious users are turning to Tor browser. Yes, but only from the sites you connect to — instead of your IP address, they will only see the IP address of a Tor server. Yes, but only as long as you download it from official sources, like Tor’s official website. Otherwise, you risk downloading fake apps that might infect your device with malware.
The Danger Of Tor Network
Nevertheless, caution should always be exercised when venturing into this hidden realm. Regular dark web visitors know that it’s possible to exploit the sketchy reputation of the space and the services offered. And though some dark web marketplaces offer user reviews, not all do. Lack of regulation by authorities or other users makes it easy for cybercriminals to carry out scams.
- Moreover, it is best to cover your webcam with tape or paper if you are not using it.
- Furthermore, it has apps for almost every operating system, including Mac, Linux, Android, iOS, Windows, and Fire TV.
- So, you should also make sure that your system’s operating system and other installed software are patched with the latest updates.
- Accessing the Dark Web, a part of the web that isn’t indexed by standard search engines, is not illegal in most countries.
Can You Use The Tor Browser On A Mobile Device?
However, we advise connecting to one of our recommended VPN services to stay anonymous. Many dark websites are perfectly legal and safe to use and, in many cases, are better for your privacy than clear websites. When you open your default browser, Freenet will be ready and running through its web-based interface.
Do I Need A VPN If I Access The Dark Web On My Phone?
By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps. To better understand how the dark and the deep web work, you must first understand how the open web operates. Web crawlers run the regular internet, scouring the web to discover newly published websites or pages in a process called crawling. Anonymizing browsers are banned in some countries like China and Russia.
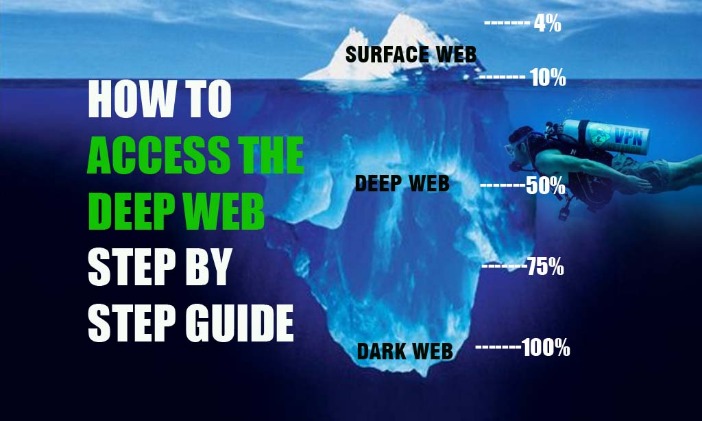
The dark web is a decentralized web, which means that the data is stored on many different servers around the world. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
Protect Yourself Against Tracking, Surveillance, And Censorship
These websites use special encryption protocols and are accessible only through anonymizing tools like the Tor Browser. If you’re having trouble accessing a website via Tor, it could be that a node, especially the exit node, has a problem connecting to the site. We discussed how some websites block Tor traffic entirely; they do this by blocking IP addresses known to be Tor exit nodes. The deep web is every part of the internet that is not indexed by search engines, like private messages from your social media or your online banking portal. The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access.
For several years, Yahoo was at the apex as the internet’s best web service provider, offering… Using a VPN with Tor (commonly referred to as “Tor over VPN” or Onion over VPN”) adds an essential layer of protection. It hides the use of Tor from your ISP and protects you if your Tor connection is compromised in some way. Using a dark web-specific browser such as Tor or I2P itself is legal in virtually all countries. But using these tools for illegal purposes constitutes a criminal act either way. Don’t be fooled into going to a malicious clone site that is designed to extract your information.
Think of it as the glossy shop windows of the internet — what you see is only what’s on display, neatly categorized and searchable. The editorial team did not participate in the creation of this guide. Gizmodo may earn a commission when you buy through links on the site.
The release of Freenet in 2000 is considered by many as the start or founding of the dark web. University of Edinburgh student Ian Clarke created Freenet as a thesis project. Freenet was originally intended to provide a way to anonymously interact online, providing ways to communicate, exchange information and files, and to otherwise communicate incognito. Identifying specific individuals who use the dark web can be quite tricky.
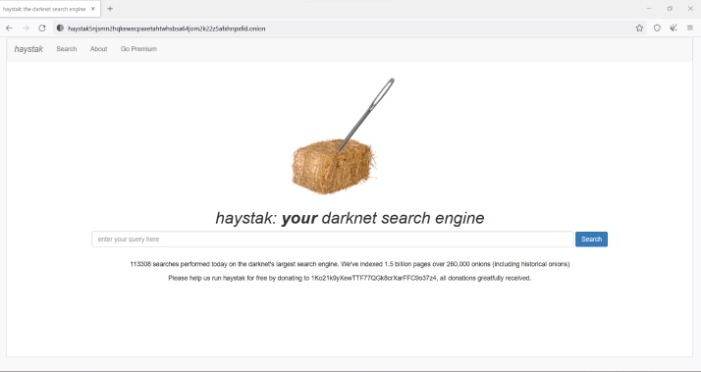
The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people). Most dark web websites are in English; according to one estimate, a staggering 78% of information on the dark web is in English. Researchers from Recorded Future estimated that while there are more than 55,000 existing onion domains, only 8,400 (or roughly 15%) of these sites were active. So, when measuring the total network of live dark web sites alongside the surface web, only about 0.005% of the internet is the dark web. Joking aside, there are some crucial steps to take if you want to access the dark web safely and anonymously.
Safety Precautions For Accessing The Dark Web
As was mentioned previously, Tor entry nodes can still see your IP address. If you want to mitigate that possibility, downloading a VPN is the best way to do so – it funnels your traffic through a private server and keeps your IP address hidden. There are plenty of services that offer a VPN over onion feature, which will keep you secure and private online. As the most widely used anonymity network, Tor routes your internet traffic through a series of volunteer-run servers (relays) around the world. This “onion” routing masks your IP address and encrypts your data multiple times, peeling away layers of encryption at each relay. Dark web sites are hidden by non-indexing, making them completely anonymous.
The network is comprised of thousands of volunteer-run servers known as Tor relays. Tor was developed in the mid-1990s by United States Naval Research Laboratory employees, mathematician Paul Syverson, and computer scientists Michael G. Reed and David Goldschlag. Tor was designed to protect American intelligence communications online. Tor Browser has since become a popular tool of journalists, activists, and others that may be subject to being monitored online.