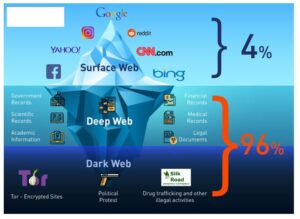
Most sites do this by deliberately placing “meta tags” in their website code to make it easier for crawlers to catalog them properly. Browsers such as Google, Bing, DuckDuckGo act like virtual librarians, sorting and cataloging materials so they can be easily searched. They do this through using “crawlers”, sometimes also known as “spiders” or “robots”. Crawlers can automatically scan websites and their links, then record them. In order to understand the dark web properly, you need to understand that the internet is a huge and sometimes disorganized place.
Is The Dark Web Illegal?
Is an independently-owned bookstore centering Black and Brown storytelling through community programming and book selling. This is a series of small books with big ideas from today’s leading activists and artists. The use of managed services by Fortune 1000 companies and large enterprises is growing rapidly. In fact, a recent study found that as many as 70% of large enterprises use managed services to support their operations. The use of managed services can help organizations stay ahead of the competition by reducing costs, improving efficiency, and freeing up internal resources to focus on growth and innovation.
The Hidden Wiki & Co
Achieving an aggressive and inspired broadband vision will help families stay connected, provide economic opportunity, increase resiliency during crises, and improve the quality of life for all Californians. We don’t want to change to a more expensive WiFi because my mom and dad aren’t working. Research indicates that average users will need speeds of 150 Mbps by 2025. However, the majority of low-income internet plans only provide speeds of Mbps today(5). When we asked people about the limitations of their internet access through only their smartphone, they mentioned missing out on career opportunities. Before he gets in the water in the beach, one of the locals takes a photo of him and Aiko.
Is Tor Illegal To Use?
The standard dark web browser is Tor Browser, which directs your browser traffic through the Tor network so you can reach the darknet. As your traffic passes through Tor, it’s encrypted and bounced between at least three relay points, known as nodes. This helps obscure the origin of the data (and makes it hard for anyone to find your IP address). But as a result, Tor Browser will feel much slower than a normal web browser.
Digital Redlining And The Black Rural South
With the Wireless NaaS solution offered by Black Box, you can enjoy the benefits of managed services without having to worry about the cost and complexity of managing a wireless network in-house. The thing about video is that the size is only limited to how much your hard drive can hold. I stopped sculpting in a traditional way because I kind of ran out of space. The thing is, the internet and Black culture on the internet is an ever-expanding thing that escapes the confines of what can be depicted in sculpture, at least in real time. When a video comes out and goes viral, I can synthesize it that same day.
Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. The deep web rests below the surface and accounts for approximately 90% of all websites. This would be the part of an iceberg beneath the water, much larger than the surface web.
Ways Small To Midsize Businesses Can Stay Safe In The Cloud
According to reports, more than 60 businesses and 100 developers use Calendly as a meeting platform to grow their firms. For years, the federal government has been responsible for developing a map on broadband access. The map tracked availability at the census block level, which a 2020 study by researchers from Princeton University found disproportionately overstated coverage in rural and minority communities. Last year, the FCC rolled out a new map using addresses, which was mandated by the Broadband Data Act.
Popular malicious tools or services also include OTP bypass bots that automate voice or SMS to steal 2FA codes, crypto drainer kits that empty victims’ wallets, and deepfake services, according to Ian Ahl, SVP at P0 Labs. It’s fragmenting into specialized communities that include credential marketplaces, exploit exchanges for zero-days, malware kits, and access to compromised systems, and forums for fraud tools. International policing groups are working to disrupt several major platforms through joint efforts. The Australian Federal Police (AFP) participated in a Europol-led investigation that in 2024 shut down LockBit’s primary platform along with 34 servers across the US, the UK, Europe, and Australia. This study involved secondary analysis of existing data and therefore is exempt from human subjects review.
Hacking Groups And Services
He realized that people didn’t necessarily want the internet to be just an information superhighway. Just how completely Tor can evade the surveillance of highly-resourced law enforcement and intelligence agencies, however, remains an open question. In early November, a coordinated action by the FBI and Europol known as Operation Onymous seized dozens of Tor hidden services, including three of the six most popular drug markets on the Dark Web. Or they may have simply used old-fashioned investigative techniques such as turning administrators into informants, or found other hackable vulnerabilities in the target sites. Omar Wasow met Benjamin Sun in the late 1990s, when they were among the few people of color working in New York City’s tech scene. After graduating from Stanford University in 1992, Wasow had moved back to his hometown and started a hyperlocal community hub and internet-service provider, New York Online, which he operated out of his Brooklyn apartment.
- It’s also used by political activists and dissidents, journalists, people who don’t trust websites’ use of their personal data, and the odd member of the tin foil hat brigade, convinced the government is spying on them at all times.
- Some of the websites to look out for on the dark web include mirrors of both the BBC and the ProPublica investigative journalism platforms, built to help inform people who are living in countries where the internet is heavily censored.
- African Americans, representing 14% of the U.S. population (47.4 million), are using unfettered access to technology as a means to broaden their reach and express themselves on their own terms.
- A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. You should stay away from everything labeled “porn”, “card skimming services”, “PayPal hacks”, “firearms”, “real fake IDs and passports”. Believe me – there are plenty to go around and each and every one of them are being kept under surveillance.
The question-and-answer session of Biden’s his first town hall meeting as president covered a host of issues. Audience member Dr. Dessie Levy’s question about racial disparities in health care prompted his comments on minority access to online health resources. Certain thematic threads run through several disciplines we publish, and the juncture of race and digital culture is one of those. Here’s a curated list of course-ready texts on Blackness and the Internet, culled from media studies, politics, and elsewhere.
More Privacy Articles
Greenlining supports SB 1130 because it would increase investment in fast, future-proof broadband networks across the state. As Senior Legal Counsel of Tech Equity, Vinhcent Le (he/him/his) leads Greenlining’s work to close the digital divide, protect consumer privacy, ensure algorithms are fair and that technology builds economic opportunity for communities of color. In this role, Vinhcent helps develop and implement policies to increase broadband affordability and digital inclusion as well as bring transparency and accountability to automated decision systems.