Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe.
In light of this, we have chosen the parameters conservatively, obtaining estimates for the number of sellers that are in general smaller than the ones produced by other methods. Second, our approach does not explicitly classify buyers, which are entities that were not classified as sellers. There is a gray zone in which some sellers and buyers may not be easily distinguishable in transaction networks.
Table Of Contents
We consider the whole ecosystem, i.e., all markets and the U2U network. In panels (b, c), we show the number of all sellers and buyers per quarter, respectively. In panels (d, e), we show the median net income in USD of all sellers and buyers per quarter, respectively.
Why Are Darknet Markets Found On The Dark Web?
Established in 2020, Awazon Market has quickly become one of the most famous darknet marketplaces. The market claims to provide secure and anonymous commerce services. You can find a lot of goods and services packed with stealth high-level encryption, no JavaScript, and anti-DDoS protection. In addition to counterfeit merchandise, MGM Grand Market offers access to stolen credit card information, compromised bank accounts, and other financial fraud-related services. Despite consistent results, this study has limitations that may be addressed in future work.
Q4 2024: Platform Expansion
In this instance, too, it is important to use a logless VPN and pay with Bitcoin if you can to stay anonymous. The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely. If you want to use Tor privately, you can use either a VPN or Tor Bridges (Tor nodes that are not publicly indexed). Tor users in the USA, in particular, may want to use a VPN, which will be faster and more reliable. Our rigorous research and testing have revealed revealing truths and busted myths.
Transparent Vendor Ratings
If it is, LifeLock will help you take steps to secure your identity and accounts. And if the worst comes to pass, LifeLock will help reimburse you for any money lost due to identity theft and provide expert assistance to help resolve your case. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools.
- They use unique addresses that end with .onion, which are not available on search engines.
- Using trusted directories, PGP encryption, and secure wallets helps protect against fraud.
- Individuals began using the darknet to pseudonymously sell illegal content without face-to-face interaction.
- This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web.
- All of this has made it one of the most reliable markets still active in 2025.
- This option is ideal for digital products, domestic shipping, and transactions with established, high-reputation vendors.
Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. Darknet marketplaces may look like regular online stores, but using or even browsing them comes with serious risks. From identity theft to law enforcement surveillance, the dangers are real — and often underestimated.
Cypher marketplace has been on the list of the best dark web shops for a while and deals with the business of a variety of products and services. The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims). To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test. Moreover, the layers of encryption and the bounce of your data from node to node effectively mask your IP address, enabling online anonymity.
Reduces Attack Surface By Disabling Unnecessary Services
Whether you chase shadows or stake your claim, this crypto nexus pulses with unseen power. Welcome to Black Ops Market, a darknet colossus carved from the digital abyss in May 2020. Fueled by the untraceable hum of Monero and shrouded by Tor’s onion veil, it stands as a fortress of shadow commerce. By February 2025, over 20,000 exchanges pulse through its cryptic grid—from coded cannabis caches to elusive psychedelics traded in hushed tones—thriving where the surface web’s clamor fades into silence. The latest version features a completely redesigned user interface with improved navigation, faster page loading, advanced search functionality, and a new mobile-friendly design. The updated interface maintains the familiar layout while adding features requested by our community.
How To Hide IP Address In 2025 (A Comprehensive Guide)
We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes. Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely. Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web. Furthermore, after a shock, the activity of buyers is resumed almost immediately, while the activity of sellers recovers more slowly. These different regimes suggest that the ecosystem’s resilience is mainly supported by the high demand of buyers rather than the response of the sellers. We classify all entities either as sellers or buyers as a function of time.
List Active Services:
Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age.
- The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous.
- There is no need to visit darknet marketplaces yourself to know whether your data was leaked.
- It has an active forum and community along with an extensive user vetting process.
- Since the dark web can be accessed through the Tor browser, use a VPN with the Tor browser to ensure increased protection.
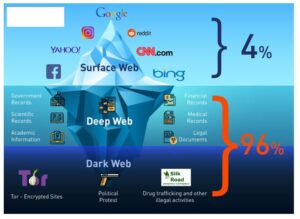
- That’s why such a large percentage (as much as 94%) of the entire web is not returned in Google Search.
Dark Web Marketplace Links
Many users value the protection that comes with keeping their identity hidden. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats. What distinguishes Black Ops Market from other darknet marketplaces is our holistic approach to security and user-centric design. Black Ops Market represents the cutting-edge evolution of darknet marketplaces, built with an unwavering commitment to security, privacy, and user experience.
Bonus: The Silk Road
You can access it for legitimate purposes like whistleblowing and freedom of expression. However, it’s also used for illegal activities like drug trafficking, weapon sales, and stolen data trading. Law enforcement agencies monitor it for criminal activities, but legitimate users rely on it for privacy protection. Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information). Even with the increase in law enforcement pressure, the dark web market still achieved a revenue of $2 billion in 2024.