Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors. Below are the best marketplaces on the dark net that we hand-picked after going through multiple shops and doing extensive research.
- Dark web marketplace links can lead to a variety of content, including educational resources, secure communication tools, and news outlets.
- Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
- You should only ever access websites you know are safe because they’re vetted by websites or other sources that you already know are safe.
- These high levels of anonymity increase the opportunity for the “bad guys” to sell drugs, stolen IDs, credit cards, weapons, and many more compromised products or information.
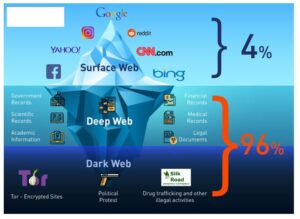
Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Estimates place the size of the deep web at between 96% and 99% of the internet. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”. The terms “deep web” and “dark web” are sometimes used interchangeably, but they are not the same. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.
One can buy credentials, credit cards, and personally identifiable information without needing to be highly technical. The organization of groups and forums are highly structured, and the specialization of roles and responsibilities are defined very well. Most of the vendors guarantee that their products will live until the promised lifespan. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers. The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud.
Why We The North Marketplace Stands Out
That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Dark web markets are home to a billion-dollar industry dealing in illicit goods. Unsettling dark web facts like this make them a great concern for governments. US agencies, like the FBI, are constantly working with international law enforcement groups to stop the growth of dark web markets around the world.
DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia. First, let me explain that this article is intended for users who want to use the dark web for legal and needed purposes, such as finding censored news, blocked websites, and other much-needed services.
Focus Friday: TPRM Actions For MadeYouReset, Ivanti Connect Secure, PostgreSQL & Plesk Obsidian
For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee.
Dangerous Fake Or Malicious Vendors
Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services. Transactions are conducted through Bitcoin and Monero which provides anonymity for both buyers and sellers.
Discover Content
- Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol.
- Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.
- Mega Market, established in 2016, experienced a surge in popularity following the takedown of the Hydra market.
- Eventually, the system collapses, and most people lose their entire investment.
- For instance, cybercriminals can buy credit card details with a $5,000 balance for just $110.
With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Cryptocurrencies such as Bitcoin have been the dark web currency even before they became available to the general public.
The market is also known for its listings related to financial fraud, such as phishing tools and stolen credit card information. Many simply install free software for enabling anonymous communication and direct internet traffic through a free, worldwide, volunteer network consisting of more than seven thousand relays. The user’s location and the usage are hidden from anyone conducting network surveillance or traffic analysis. Most of these free software options make it more difficult for Internet activity to be traced back to the user, including website visits, online posts, instant messages, and other communication forms. In exploring the top 10 dark-web marketplaces in 2025, we’ve examined their core operations, diverse use-cases, inherent risks, and evolving trends.
How To Access The Dark Web
Enable MFA wherever possible to protect your accounts from unauthorized access. This space for private free speech also carries the risk of exposing you to harmful content. Hidden Answers is one of the biggest question-and-answer dark web sites. This makes Riseup a vital tool for people in oppressive environments or anyone concerned with online privacy. However, Ahmia doesn’t have a large developer supporting it, so it’s been the target of scams or cyberattacks in the past.
Archived Content
This website is made public with the intention to aid the Internet users with navigation of the so called dark web. We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. 7, we show the largest component of the S2S network one year before the operation Bayonet and one year after.
What Could I Buy On Silk Road?
It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. It works by sending internet traffic through volunteer-operated nodes all over the world.

{The seizure of Bitcoin and arrest of Ulbricht were meant to send a clear message to other cybercriminal enterprises. Arraignments in federal court in Chicago have not yet been scheduled. } mark it means it has been verified as a scam service and it should be avoided. This feature is satisfied when \(\phi _i(t) \le \tau\), where \(\tau\) is the maximum value of mean interevent time.|Cybercriminals can rent or buy malware tools through darknet markets. This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves. Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files. Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return. Once you send the money, there’s no support team to get it back. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach.|The U2U-only category is comparatively small, representing only 6% of all buyers on average. The number of market-U2U and market-only buyers also drops as a consequence of operation Bayonet. However, compared to sellers, the drop is notably smaller, and the number of buyers rapidly recovers to previous values. On the other hand, the number of U2U-only buyers is less affected. Moreover, the number of multibuyers increases, which suggests a fast response from buyers to external shocks by trying to diversify their sources. Typically, you can find dark web URLs through forums, databases, or by talking to others who frequent those sites.|Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.|Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Wherever you go online, but especially if you’re on dark web websites, using a VPN helps you secure your communication data and protect personal information you send or receive.}
The New York Times — Globally Recognized News Coverage
I actually ended up asking a friend who studied computer science to come over and help, as he had experience with the marketplaces. I never talked to that man again but that experience really set in stone the steps I needed to take that would lead me to several tens of purchases. Blockchain technology is a decentralized digital ledger that records all transactions across a network of computers. It’s most notably used for cryptocurrency transactions, ensuring transparency and security without the need for a central authority. What’s submerged is the deep web — an anonymous online space only accessible with specific software. Then there’s the dark web, which is the part of the deep web that hides your identity and location.
Keep in mind what you’re looking for, find that information, and disconnect from the dark web. As enticing as it might be, don’t follow links to other parts of the dark web. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. In opennet mode, the network will automatically assign you to other users on Freenet’s network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.