This means you should never change the default settings in the Tor Browser. The folder will be named “tor-browser_en-US” if you are running the English Tor Browser. Open the Downloads folder on your Mac, and double-click the file you just downloaded. Simply visit the Tor Project website, then click on the “Download Tor Browser” button found in the upper right-hand corner or the center of the web page. The Tor Browser is a modified version of the Mozilla Firefox browser and includes the TorButton, TorLauncher, NoScript, and HTTPS Everywhere Firefox extensions, along with the Tor proxy. Upon selecting the button for your operating system, you will be prompted to download the installer, which you should save to a folder.
Install TAILS
The platform is protected from government interference and malicious attacks to protect the user. In addition, it ensures that no record of communication is stored. There are different levels of security in the browser that are worth considering.
Protecting your personal information should be your priority when using the dark web. Don’t share sensitive details, such as your name, address, phone number or financial information, with anyone. Doing so could lead to identity theft or other forms of cybercrime. Maintain a high level of anonymity by using pseudonyms and encrypted communication whenever possible. Remember, while the dark web hosts a range of content, accessing illegal materials or services is, well, illegal.
First, Install A Reliable VPN
Unfortunately, some oppressive regimes have figured out a way to block Tor traffic. Tor Over VPN is when you first connect your computer or mobile device to your VPN service and then use the Tor Browser to travel the internet. While the Tor Browser does an excellent job of protecting your privacy and anonymity, you really shouldn’t use it as your daily driver browser.

Popular Dark Web Search Engines
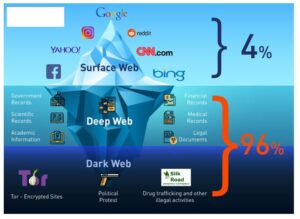
The dark web, by contrast, is configured on darknets — online networks that can be accessed only with special software and techniques. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. It is easily accessible by the general public and requires no special configuration.
- While Tor lets you reach .onion sites, many require invitations, passwords, or verification.
- Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
- The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users.
- If you need to create accounts on dark web services, use a burner email and never reuse usernames or passwords from your real life.
- In addition to standard websites, there are also servers that are only accessible through the Tor browser.
- The wizard will guide the user through a series of steps, including selecting the preferred language and choosing an installation location on their computer.
What Is Tor?
Plus, some people still don’t know how to get and use the Tor browser, despite it being pretty accessible and user-friendly. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing. Many dark internet users favor Tor which uses a network architecture originally developed by the U.S. Naval Research Lab as a system of decentralized, anonymous nodes to enable anonymous online communication.
Don’t Reveal Any Personal Information
You can use the VPN rated #1 for the dark web with no restrictions for a month—great if you want to try this no-log provider’s Onion over VPN servers for yourself. The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations.

There is only one official download site for the Tor browser, and that is torproject.org. Builds of the browser are available for Windows, MacOS, Android and Linux systems. Standing for The Onion Protocol, Tor is a system of network encryption designed to protect your privacy and help you stay anonymous online. The dark web is made up of a variety of different overlay networks and accounts for somewhere between 5-6% of the overall internet.

It has been estimated that a large percentage of dark web traffic is related to illegal pornography that includes underage victims. Hacker services against banks and other financial institutions are offered there. There are a number of services and tools available on the dark web, many of which can be used for nefarious purposes.
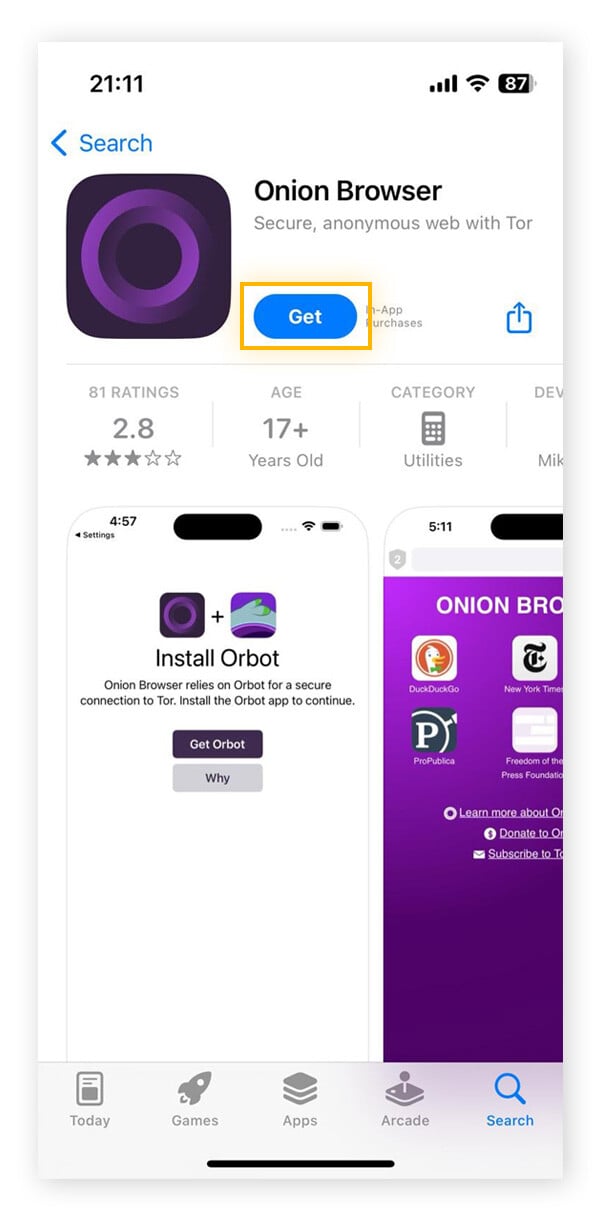
Step 5: Start Browsing Hyphanet
With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. DuckDuckGo is the default search engine inside the Tor browser, and once you turn on the Onionize toggle switch in the search box, you’re able to use it to find dark web links. These typically come with “.onion” after them, rather than something like “.com” as on the standard web. Tor is like the public-facing door to the dark web, and there are even mobile apps for Android and iOS. On the surface web, you can contact your credit card company or law enforcement for help.
Disgruntled Developer Gets Four-year Sentence For Revenge Attack On Employer’s Network
If you’re new to Tor, setting up the browser software and connecting to the network might seem intimidating, but it’s actually straightforward. We’ll guide you through how to connect on Windows, Mac, Android, and even iOS. You can download the Tor Browser for free from its official website at torproject.org. Be sure to only download it from the official site to avoid fake or malicious versions.
Also, it is worth noting that using Tor may draw attention from authorities if they suspect you are engaging in illegal activities or if your online behavior raises suspicion. Generally, it’s important to use Tor responsibly and in accordance with local laws and regulations. Fortunately, it’s not a criminal offense if you simply search the dark web, but if you use it to carry out illegal activities, you get in trouble.
- Since its public release, researchers have discovered various vulnerabilities in Tor, which have been quickly patched.
- Since their deadline wasn’t met for the closer of the sites a month later, the Impact team ascended to the dark web, where they started to publish the data.
- Using the internet anonymously is becoming increasingly important in today’s surveillance-driven world.
- Data privacy is one of the major civil rights issues of the 21st century, and it’s just smart to keep a lock on how much people and corporations know about you.
The Tor Browser is the safest and most trusted way to access the dark web. That said, there are still some ways to protect yourself when using the Tor Browser. Dark web browsers rely on complex encryption protocols to route users’ connections through multiple servers, making it nearly impossible to trace activity back to the original user. Most dark web browsers use The Onion Routing (Tor) network, where data is encrypted in layers and sent through multiple nodes. This “onion” structure helps keep user identities secure while they browse the dark web.
It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites. RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.