But using these tools for illegal purposes constitutes a criminal act either way. Downloaded files could have malware in them that may be designed to de-anonymize you or infect your device. If you must download something from the dark web, only download files and run them using a completely isolated virtual machine.
With Tor, you don’t have to worry about comments coming back to haunt you, or your internet history being tracked. The Tor community keeps Tor running, but no top-down authority has access or control of the data. Tor is not itself illegal, but much of the activity on the dark web is illegal.
Dark Web Access Guide: How To Enter The Dark Web Safely
- The dark web serves as a common platform for cybercriminals to distribute various types of malicious software designed to compromise users’ devices and steal their personal information.
- This Tor-based browser is commonly used for surfing anonymously and comes with pre-installed Qubes for extra privacy.
- Each node in the Tor circuit only knows the IP address of the node directly before and after it, never the entire path.
- VPNs, proxies, and alternative privacy-focused networks like I2P and Freenet also offer unique advantages.
- Using Tor with a VPN adds an extra layer of protection by masking your IP from the Tor entry node.
- In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network.
While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking. For searching within the dark web, specialized tools like Torch are better, as they specifically index .onion sites and hidden content. It’s simply a part of the internet that isn’t indexed by regular search engines and needs special software, like Tor, to access. However, while browsing the dark web itself is lawful, taking part in illegal activities — like buying or selling illegal goods or engaging in criminal behavior — is not. To stay on the right side of the law, be cautious about what you access and ensure you follow the rules in your region.

Downloads
Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity. People often have bad feelings about the dark web, but not everything on it is illegal or dangerous. In fact, journalists, privacy advocates and academics use it every day to protect their identities and get to material that has not been blocked. There are alternatives to Tor, including the Invisible Internet Project (I2P), Lokinet, and Psiphon. Research what they offer and assess your privacy needs to make a decision about which dark web browser works best for you.
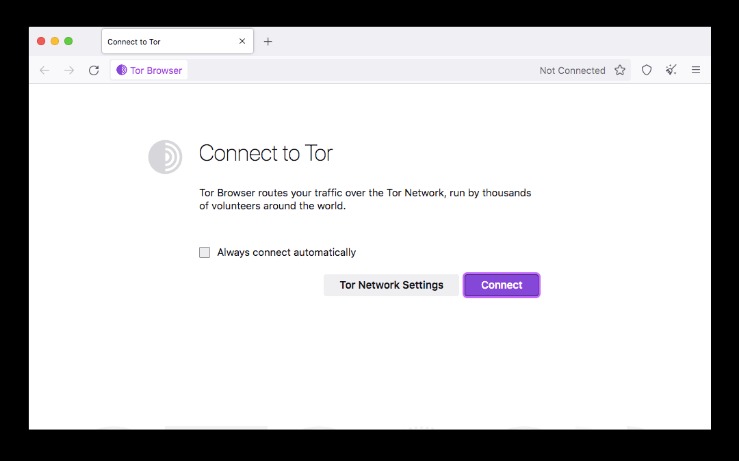
How To Set Up & Use The Tor Browser
When the final layer of the “onion” is reached and decrypted, the message arrives at its destination. These URLs are usually very long, consisting of a random jumble of letters and numbers. Though you likely won’t remember the addresses of onion websites, you can find these URLs on various websites on the internet.
Make Simple Software Security Checks Part Of Your Purchasing Process
The dark web is a small section of the deep web that is hidden on purpose, requiring specific software to access. Furthermore, it is strongly recommended to avoid downloading any files from the dark web unless absolutely certain of their safety and origin. The dark web is a known haven for the distribution of malware, viruses, ransomware, and keyloggers, which can severely compromise a user’s device and personal data. Even seemingly innocuous files could contain malicious payloads. Similarly, engaging in financial transactions or making purchases on the dark web is generally discouraged due to the high risk of scams and potential legal ramifications.

Top 10 Best Dark Web Search Engines In 2025 Safe &
Go to the directory where you downloaded the Tor Browser installation file. Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been extracted, double-click on “Tor Browser Setup” to install the browser. Go to the directory where you saved the downloaded Tor Browser installation file.
Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS. People mostly use it for covert communication, anonymous tips submission, and stuff like that. In terms of functionality, I don’t think there are too many differences between regular IMAP, POP3, and SMT services and the stuff you can use to communicate on the dark web.
Step 6: Advanced Hyphanet Features (Optional)
Tor Browser works by sending a data packet through an entry node, a randomized relay node, and a randomized exit node. Staying safe on the unregulated dark web requires vigilance, and its seedy reputation, fostered by controversy like that surrounding Silk Road, is well-earned. Understanding the Dark Web and its access tools, such as Tor, is crucial for anyone considering exploring these hidden parts of the internet safely and responsibly. For the utmost privacy and security, combine Tor with a VPN connection.
Top DEF CON And Black Hat Talks Of All Time
- Since Hidden Wiki maintains all kinds of websites, ensure you don’t open something you don’t want to see.
- Deep Search is an open-source dark web search engine designed to index and explore onion space, the hidden services within the Tor network.
- It is difficult to track the online activity of users because it routes traffic through a network of servers.
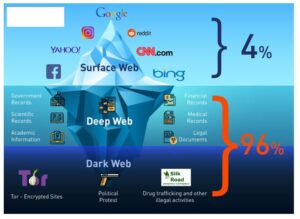
- Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
- However, they might not index as extensively as Clearnet search engines do for the regular internet.
Haystack doesn’t track or store your search queries or personal data, which is critical to maintaining anonymity on the dark web. This aligns with the general ethos of privacy on the Tor network. Haystak boasts an impressive index of over 1.5 billion pages from more than 260,000 websites on the dark web. It offers both free and premium services, with the premium version providing additional features and more detailed results.
The best thing is to actually understand how to find the fresh, new links. Formerly known as Archive.is, it is one of the best onion sites on the dark web. It aims to preserve the internet’s scientific and cultural heritage. This service is a good source of statistics if you have a school project requiring research on Tor and the dark web. However, note that the site only uses non-sensitive and public data for the metrics.
Tor provides anonymity through a process known as “onion routing,” where internet traffic is encrypted and passed through multiple network nodes. Each node decrypts just enough data to know the next destination but not the origin, making tracing the connection back to the user exceptionally difficult. Dark web browsers rely on complex encryption protocols to route users’ connections through multiple servers, making it nearly impossible to trace activity back to the original user. Most dark web browsers use The Onion Routing (Tor) network, where data is encrypted in layers and sent through multiple nodes. This “onion” structure helps keep user identities secure while they browse the dark web. Once Tor Browser is successfully connected to the Tor network, users can begin to explore what are known as onion services, often referred to as websites on the dark web.
Users need to be cautious about the websites they visit and the files they download. Furthermore, deanonymization may be possible as a result of browser flaws. Epic Browser, staunchly committed to privacy, integrates built-in proxy support. It facilitates access to select dark web content through global proxy servers. Here, we provide the top ten darknet browsers of 2023, which have been carefully compared to industry standards for privacy, security, and usability. Downloading tainted files or clicking suspicious links can install malware on your device, so be cautious when surfing the web.