However, criminals and malicious hackers also use the dark web to hide their illegal activities. It is designed to provide online anonymity and privacy to its users. Journalists, activists, and individuals concerned about online privacy and security often use it. The dark web is a hidden part of the internet that can be accessed through limited resources. Moreover, you need to be more cautious while accessing it, as without proper safety, you can fall into the wrong hands and face serious consequences. Following are important tips you need to remember while visiting this dark part of the web.
WANT TO TRY THE TOP TOR VPN RISK FREE?
- Setting up Tor correctly is critical if you want to browse the dark web without exposing your real identity.
- To use a new circuit, click the circuit button next to the domain.
- Likewise, you’ll experience slower browsing speeds when browsing via Tor, as your requests get bounced through several servers before being processed.
- The user will have the discount automatically applied after they click on it and check out.
- Law enforcement agencies frequently target sites that distribute child pornography.
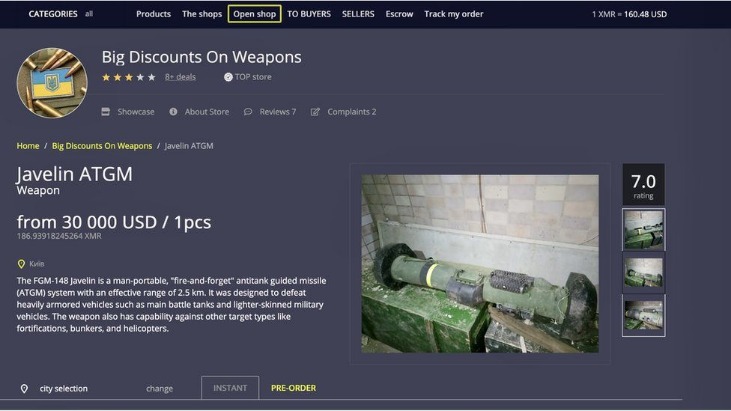
Jurisdictional differences significantly impact the legal interpretation and enforcement of dark web activities. The global nature of the internet means laws and penalties vary widely between countries, creating a complex legal landscape for users and law enforcement. Understanding these differences is crucial for cross-border investigations or cases. Illegal content on the dark web extends beyond tangible goods to digital products like malware, hacking services, and counterfeit documents. Law enforcement agencies have increased efforts to shut down these markets. Operations like “Operation Onymous,” which led to the seizure of over 400 dark web sites, demonstrate the ongoing battle against criminal content.
How To Access The Dark Web Safely: A 2025 Beginner’s Guide
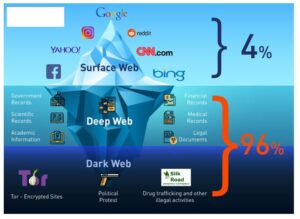
The chances of opening websites with malicious, inappropriate, or illegal content are very high, especially if you don’t know the exact .onion website you wish to visit. You will never know when you stumble upon illegal materials, inadvertently download malicious software, or expose yourself to identity theft. But if you must visit the dark web for ethical reasons, here are some safety precautions. Now, before the security tips, we’ll first figure out what the dark web is. The dark web is that part of the internet not indexed by search engines such as Google.
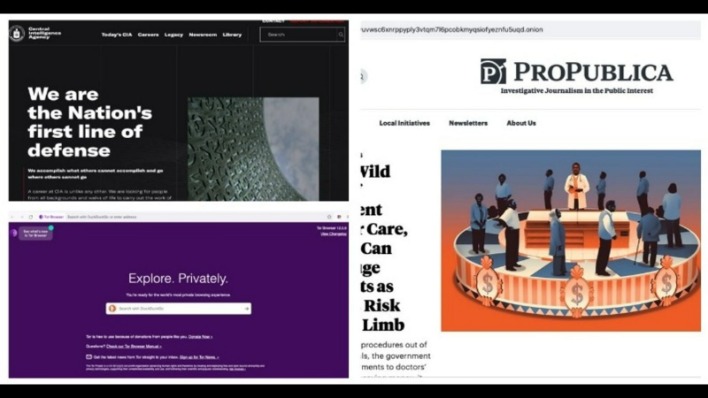
A Dark Web Search Engine
Still, Tor has gotten quite a bit faster over the years, and with a good internet connection, you can even watch YouTube videos over Tor. The following are key risks of accessing the dark web you should be aware of. The dark web also offers access to blocked resources in countries with strict government censorship on the internet. Citizens of such countries can use the dark web to bypass firewalls and access global information. The dark web exists to provide users with anonymity and privacy on the internet. Some users, such as whistleblowers or journalists working on sensitive issues in oppressive authoritarian governments, need privacy to carry out their activities.
Government Surveillance
While this is not much compared to standard email services, it is enough for PGP-encrypted messages. ProtonMail is a Swiss-based email service that is very easy to use. You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted.
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN.
VPN Over Tor
Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page.
Accessing The Dark Web Without Tor: Setting Up I2P And Hyphanet
The so-called surface web is readily accessible to all of us and thereby, less interesting. Well, relying on Tor to keep you anonymous online is a good recipe for disaster – we’ll see why soon. Furthermore, the dark web’s reputation often attracts curious individuals who are unaware of the potential risks. Casual exploration can lead to exposure to malware, scams, or illegal content, any of which could have severe consequences, both digitally and legally.
Flare Network Partners With Everything Blockchain To Integrate XRPFi For Institutional Yield Management
There are multiple search engines on the dark web that can help you find what you’re looking for. DuckDuckGo’s no-track dark web search service can be accessed in the Tor browser and is an excellent resource for information about the dark web. Other dark web search engines include Not Evil, Torch, Haystack, and Ahmia.
The Role Of Law Enforcement
NordVPN has a strict no-logs policy to ensure user privacy and employs 256-bit AES encryption. It is also available on various operating systems, including Linux, Windows, MacOS, iOS, and Android. However, it’s important to note that NordVPN can see your traffic details before encrypting them, even though it does not keep logs.
The internet is huge—even in its shadows—it is possible to wander legally there. Microsoft Word is one of the best word processors around, allowing you to craft powerful documents with an intuitive interface. If you know how to use Microsoft Word, you’re typically working with large files that span multiple pages.
Traders cash in on stolen credit card data dumps, initial access points to vulnerable systems, credentials, and intellectual property belonging to companies compromised during cyberattacks. The dark web, however, requires special software to access, as explained below. The area of the internet we access daily is known as the clear or surface web.