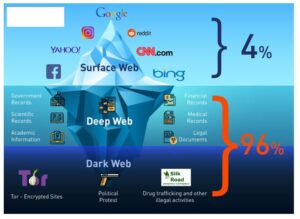
The process is structured similarly across most dark-web marketplaces and generally includes using privacy-focused cryptocurrencies, anonymous communications, and secure delivery methods. Thousands of vendors advertised goods and services on Empire Market, including controlled substances, compromised and stolen account credentials, stolen and counterfeit credit card information, and counterfeit currency. The controlled substances sold by vendors on Empire Market included heroin, methamphetamine, cocaine, LSD, opioids, and others. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. Darknets and Dark Web sites are encrypted, peer-to-peer networks that are only accessible via certain tools. Most Dark Web users use the TOR browser, which is designed to make the Dark Web easier to navigate.
Why Security Leaders Prefer To Buy CTI Solution For SaaS Platforms In 2025

This proactive monitoring enables businesses to track and investigate potential threats in real-time, helping to prevent fraud before it can impact their operations. The use of such platforms is crucial for maintaining the integrity and security of customer data, and it provides an additional layer of defense against cybercriminal activities. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web. However, you can find legitimate content and activities here, too.
The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
What Are Autoshop Marketplaces
However, I’ve come across many sketchy looking shops and marketplaces throughout my exploration, and I wanted to know “how legitimate” these sites are? The ones that sell drugs, firearms, hacked Netflix accounts and all that. I’m going to assume a lot of them are fake when they only accept Bitcoin as payment knowing it’s hard if not impossible to track back, but I’m genuinely curious as to how real these places are. Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is one of the most notorious credit card shops on the dark web. It has built a reputation for being a reliable source of stolen credit card data and PII.

Technical And Legal Risks Of Buying And Using Fake Documents
ZeroBin is a wonderful way to share the content you get from dark web resources. It is a reliable messaging tool where you copy/paste a text or image and send it to your addressee. In most cases, whistleblowers have sensitive information about the government or a company. They can be easily traced and even prosecuted if they share the information on the surface web. SecureDrop is a site that protects the privacy of journalists and whistleblowers. The website is available on the surface web and has a .onion site.

Preventative Measures And Protecting Your Identity From Fake Document Fraud
Fake IDs and fraudulent documents refer to identity materials produced or altered illegally, which are widely traded through the hidden marketplaces of the dark web. These counterfeit documents include driver’s licenses, state identification cards, passports, social security cards, birth certificates, visas, and even professional certifications or diplomas. The dark web, a concealed portion of the internet accessible only through specialized software like Tor, provides an ideal platform for such illicit trade due to the enhanced anonymity it offers buyers and sellers. This underground marketplace thrives on anonymity and cryptocurrency transactions, making it particularly attractive for those seeking to conceal their identities or bypass legal restrictions. Despite their allure, these fraudulent documents come with substantial risks, both legally and personally.
Types Of Dark Web Sites (and What Really Goes On There)
H25.io is a premium directory in the Tor network, offering access to a diverse and meticulously curated list of onion sites. Our mission is to simplify navigation in the complex and evolving world of the darknet. Here, you’ll find links to various resources, including educational archives, private forums, anonymous services, and more. Beyond abstract ethical considerations, document fraud frequently results in direct harm to individuals. Identity theft victims, for instance, suffer severe personal, financial, and psychological damage, often spending years attempting to restore their credit histories, reputations, and emotional security.
Is It Illegal To Order Counterfeit Money With No Intention Of Spending?

He explained to Elliott that he relied on cash because he was an investor in a marijuana business that was prohibited from using banks. The fakes — reproductions of $100 bills phased out in 2013 in favor of a harder-to-fake currency — had been printed on high-quality laser printers and specialty paper. The dark web’s backbone is a system called the Onion Router, known as Tor, a network of software and online connections that mask those who use it. Tor has attracted both criminal and legitimate users — political dissidents overseas, for example — seeking to avoid government surveillance. Britsch knew he had struck gold when he found Billmaker, the online moniker of an anonymous counterfeiter who promised a high-quality $100 bill and a money-back guarantee. He even had a loyal fan base who praised his work and customer service with scores of positive reviews.
One of the most significant barriers to finding deep and dark web sources is that you must use the exact URL to access sources that are not indexed — even with a browser like Tor. For example, to access the popular dark web forum CryptBB, you must know the exact onion link; conducting a web search for the forum will not turn up anything useful. Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site. Some well-known underground sources can be easier to find because there are dedicated sites that share links and maintain regular status updates. But in many cases, finding the exact URLs through manual search methods can be next to impossible.
Societal Impact Of Document Fraud
It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. The use of the dark web raises suspicion as it shows there is something you want to do privately. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. For this reason, you must watch out and avoid opening anything that looks suspicious to you. All in all, it is not illegal to access the dark web, but it can create issues for you.

For several years, Yahoo was at the apex as the internet’s best web service provider, offering… In today’s digital era, where information is constantly on the move across all digital platforms, an… If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic.
- You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials.
- Authorities employ advanced data-mining software, network analytics, and artificial intelligence-driven algorithms to detect patterns indicative of illegal trade or fraudulent document production.
- The dark web, a concealed portion of the internet accessible only through specialized software like Tor, provides an ideal platform for such illicit trade due to the enhanced anonymity it offers buyers and sellers.
- The price tag for these items may be surprising, with usernames and passwords selling anywhere from $.10 to $1 and fingerprints selling for about $2 each.
- Johnson had served three years in federal prison for selling pirated copies of Microsoft Office.
Or if you have any other ideas of how to make good use of these in my country. After looking at all of the receipts, additional agencies were contacted because they indicated the counterfeit money was passed at many other locations. CRENSHAW CO., AL (WSFA) – Clerks at a Brantley store are being credited with helping stop a multi-state counterfeit money spending spree.
Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Many services that are allegedly offered on the dark web are scams.