
Such models ensure that the market remains community-controlled and resilient to outside interference. Experienced blogger with a strong focus on technology, currently advancing towards a career in IT Security Analysis. I possess a keen interest in exploring and understanding the intricacies of malware, Advanced Persistent Threats (APTs), and various cybersecurity challenges. My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics.
The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. I2P can only be used to access hidden sites that are only available on the I2P network. As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others.

Silk Road And Early Markets
Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all. A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch.
Emerging Darknet Marketplaces Of 2025 Anatomy Tactics & Trends
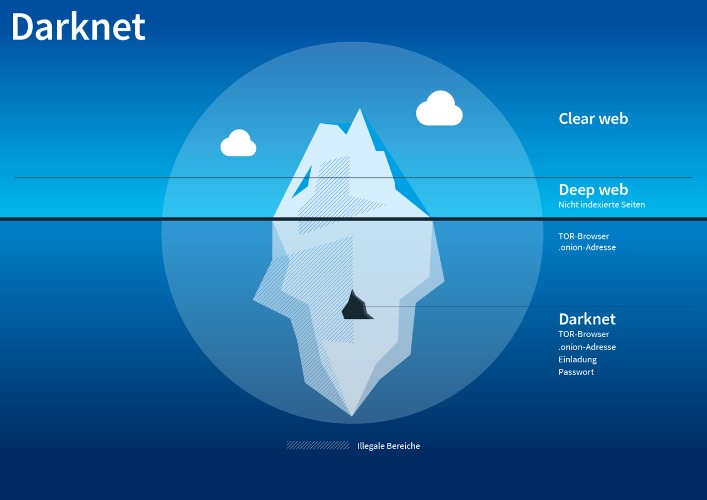
When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website. Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name. Let’s get this straight — not everything on the dark web is illegal or harmful. In fact, some parts of it actually provide a safe space for privacy and freedom, especially where traditional internet access is limited or censored. In adherence to the Trust Project guidelines, BeInCrypto is committed to unbiased, transparent reporting.
The list of the offered on-the-market drug data was gathered from the “darknet market” Hydra, along with the volume delivered and region of the offer. The data were collected using advanced web scraping techniques to extract specific information on drug types, quantities, and corresponding regions. These platforms, operating within the Onion Router (TOR) network (a network that allows anonymous browsing), are anonymous and transient; therefore, specific market names are omitted. Onion sites can be safe in terms of privacy protection due to strong encryption, but they also host a significant amount of illegal content and scams. It’s important to only visit trusted sites and avoid clicking on suspicious links. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
This adaptable approach ensures that our results can be harmonized for future comparison, providing a comprehensive understanding of the drug market dynamics. In the next step, we have meticulously gathered official data on Russian regions from the Ministry of Health of Russia, police reports, court reports, and the prison system 27. Figure 1 presents the comprehensive cycle of collecting, modifying, and analyzing data at every step, ensuring the utmost accuracy and reliability. The pathway of the data collection, cleaning, transforming, classifying by drug type, and disaggregating by the regions is presented in Figure 1. Ultimately, this disruption to accessibility is not a unique event.
Best Dark Web News Sites Offering Factual Information
- It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
- This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located.
- Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement.
- Usually these products are sent to the buyer by post and money transferred to the seller through the escrow system.
- As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
- Wasabi is one of the most popular cryptocurrency wallets on the dark web.
In fact, it is routine for individuals participating in these dark web communities, par for the course of engaging in the markets. But those of us who have studied this space for years weren’t surprised. But shutdowns like this have become a recurring feature of the dark web. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. These domain names are not registered with a central authority but are instead derived from cryptographic keys.
Association Of Drugs For Sale On The Internet And Official Health Indicators: Darknet Parsing And Correlational Study
All your traffic is automatically routed through the Tor Network. Ensure you download the Tor Browser from the official website to avoid downloading malware, spyware, or other viruses to your device. As long as users take the necessary precautions, no one knows who anyone else is in the real world. Users’ identities are safe from the prying eyes of governments and corporations.
History Of Dark Web Marketplaces
Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets. Due to being the most popular and the oldest coin, Bitcoin is traceable.

Some even have connections to criminal organizations and, in more serious cases, government-backed operations. In many countries, strict laws limit who can legally buy, own, or carry firearms. The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection.
Torzon Market
Another great source to find and explore dark web marketplaces or other sections is to visit Reddit’s resourceful forum. You can look for information on /r/deepweb, /r/TOR, or /r/onions, of which the latter is useful to find hidden wikis and more. Many of these Reddits have rules prohibiting linking to illegal sites and services, so you likely won’t find anything illegal there.
- Taking the necessary precautions makes tracing your activities on the dark web difficult.
- Journalists and whistleblowers, including Edward Snowden himself, often use the dark web and Tor to exchange sensitive information.
- Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results.
- Certain details of your traffic can be intercepted at the entry and exit points of the node, by the people running those nodes, if they know what they’re doing and what they’re looking for.
Just like in the old days of the internet, the dark web maintains numerous indexes of sites, like The Hidden Wiki. Unlike Ahmia and Haystak, however, DuckDuckGo doesn’t search .onion sites. Use it to search the normal internet from the privacy of your Tor Browser. Haystak also offers a premium version that allows advanced search, access to historical content, and email alerts. The three nodes separate your IP address from your destination and enable two individuals to communicate without either party, or any middleman, knowing who the other is. Needless to say, it takes your data much longer to travel this way, which means dark web links load slowly compared to indexed sites.
Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. Unlike regular browsers that directly connect to websites via your ISP’s DNS, Tor anonymizes your journey by routing your request through several relays before reaching its destination.
Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. Blockchain even has an HTTPS security certificate for even better protection. The role of the darknet in the drug trade has substantially grown over the last decade. With the advent of the Silk Road, the first darknet marketplace, customers and vendors have collaborated to disseminate and acquire goods and services that were previously unavailable digitally 5,6.



