Even browsing these sites can put you at risk of malware infections or attract unwanted attention from law enforcement. Abacus Market is one of the newer darknet marketplaces that quickly filled the gap left by AlphaBay’s takedown. It hosts over 40,000 listings and offers everything from illicit goods and substances to hacking tools. With an estimated market value of around $15 million, it has grown into a massive hub for cybercriminal activity. The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots. These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going.
Table Of Contents
The marketplace has a pleasant, user-friendly interface built from the ground up. Its interface makes it easy to identify clone websites and ensures that users always use the authentic site. The browser uses onion routing technology to route the internet traffic through multiple relay nodes that provide layered encryption. The layers of encryption hide your data and activity from snooping eyes. Russian Market has consistently remained one of the most popular and valuable data stores on the dark web.
How Do Dark Web Markets Work?
Stay informed, make responsible choices, and never engage in any illegal activities. By doing so, you can explore the Dark Web on your iPhone while staying within the boundaries of the law. Explore a diverse selection of goods and services, with a focus on privacy and security. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity. That’s why we always recommend using a VPN over Tor—even if you feel you have nothing to hide. This just involves turning on your VPN before you open Tor and connect to dark web sites.
Top 7 Dark Web Marketplaces
The advantage of using a dedicated computer just to browse the dark web is that your main computer isn’t exposed to any of the threats or risks tied to entering the dark web. In case of an attack, you can be sure that any of the data or information stored on your main computer will be safe. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website.
Finding The Real Nexus Onion Link
STYX Market focuses specifically on financial fraud, making it a go-to destination for cybercriminals engaged in this activity. However, the dark web is so complex and vast that if law enforcement takes down one market, it pops up elsewhere. For instance, after the closure of Genesis Market, its website came back after a few weeks. If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding. Like ransomware, criminals can buy software and inject your devices with viruses.
Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of. In fact, several businesses can use that service to get rid of competitors, or individuals can use it to gain access to personal information about someone. To remain anonymous about your purchases on the dark web, always use cryptocurrency as your mode of payment. If a seller encourages you to opt for other well-known and commonly used payment methods, then the person is likely to be a scammer, and you must not make any deal with them.
How To Access Onion Sites
While there is no official Tor browser for iOS, there are a few third-party options available. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily.
While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. Cryptocurrencies, while offering enhanced privacy, also present significant risks. Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions. Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users. An intuitive, user-friendly interface is crucial, especially given the complex nature of dark-web interactions.
The Full List Of Trusted Darknet Markets:
However, remember to proceed with caution and follow best practices to protect your privacy and stay safe while browsing the Dark Web. These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge.
Plus, it includes a built-in, bank-grade VPN to encrypt your connection and help keep your communications more private. While the spyware was designed as a tool to help law enforcement crack down on terrorism, drug trafficking, and other crimes, in practice, it has also been used on innocent whistleblowers. Finally, Pegasus exfiltrates data to attacker-operated command and control servers. Attackers can use the information to track the target’s activities, gain further insights into their personal and professional life, identify their contacts and networks. Once Pegasus infiltrates a device, it can harvest a wide range of data by accessing the phone’s operating system, applications, and memory storage. Track and analyze darknet activities using our advanced cyber threat intelligence platform to stay ahead of emerging threats.

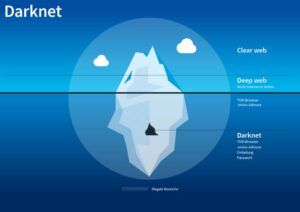
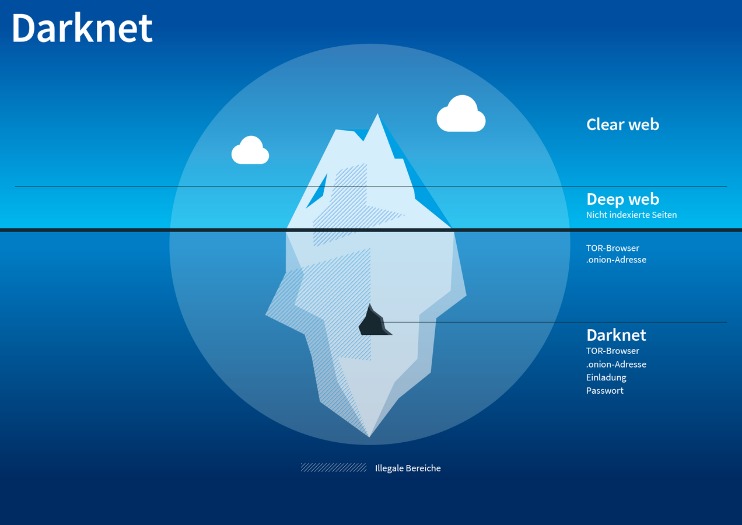
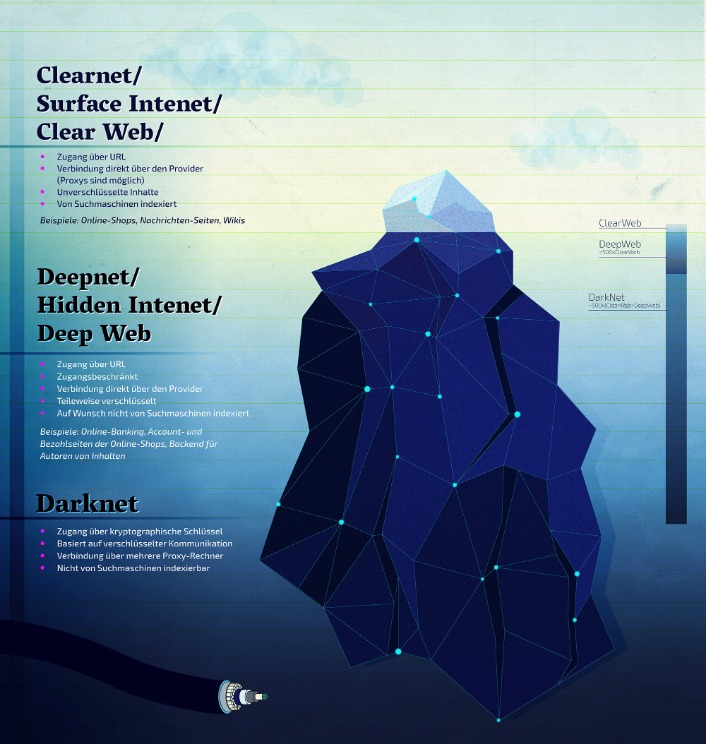
It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet. The dark web and the deep web are often used interchangeably, but they’re two distinct concepts. To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017.
- When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
- It has an active forum and community along with an extensive user vetting process.
- Keep in mind what you’re looking for, find that information, and disconnect from the dark web.
- Remember, the Dark Web is a risky place, and it’s essential to proceed with caution.
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets

Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. Shop for exclusive products in our marketplace, where privacy, security, and anonymity are always a top priority. It is not recommended to access the darknet without a VPN, as it can leave you vulnerable to surveillance and hacking. A VPN will help to protect your privacy and security by encrypting your internet connection and routing it through a server in a location of your choice. As an experienced copywriter, I understand the importance of rewriting content in an engaging and informative manner. Both Brave and Tor browsers provide adequate protection for privacy-conscious users, but they have different approaches.
This mechanism holds funds in a secure account until the buyer confirms receipt of the product, reducing the risk of fraud. Additionally, multi-signature transactions are increasingly common, requiring multiple parties to approve a payment, further enhancing trust between users. These features collectively create an environment where the drug trade can thrive securely and efficiently, meeting the demands of a growing user base. The evolution of darknet markets in 2025 demonstrates their ability to adapt and innovate, ensuring their continued relevance in the digital age. One of the key factors contributing to the success of these markets is the use of onion addresses.
Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?). It also offers works of art, course material, and audiobooks for download. Impreza Hosting is a service that helps you host a site on the Tor network. It provides an .onion URL and an interface for you to manage your Tor site easily. It also boasts that no personal information is required to use the service, and payment can be made with cryptocurrency. Pastebins are text sharing services, useful for sending and sharing large snippets of code or text.

The Tor browser comes with three layers of security that are worth considering and using. Go to the Advanced Security Settings option that’s accessed by clicking on the Shield button. The most important thing is to ensure that you never click on links that you’re not sure of their source. Also, it should be common knowledge not to share personal information online. Perhaps, the figures can tell you what your personal information is worth when it lands on the dark web.