These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information. The second category consists of data stores, which specialize in stolen information. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. In 2023, the dark web attracted an average of 2.7 million daily users, with Germany now leading as the country with the highest number of Tor users, surpassing the United States for the first time in years. Learn how to make money using the Lightning Network and the risks, and explore opportunities to monetize your… The ability to integrate LN with other blockchains and expand functionality will take the network to a whole new level.
Darknet Markets 2025 – Your Deep Web Roadmap

When considering cryptocurrency exchange rankings, though, both of these types of businesses (exchanges and brokerages) are usually just thrown under the umbrella term – exchange. Reading through various best crypto exchange reviews online, you’re bound to notice that one of the things that most of these exchanges have in common is that they are very simple to use. While some are more straightforward and beginner-friendly than others, you shouldn’t encounter any difficulties with either of the top-rated exchanges. That said, many users believe that KuCoin is one of the simpler exchanges on the current market. More often than not, law enforcement is targeting the sellers more than the buyers.
Saved Searches
Multi-signature escrow, end-to-end encryption, and mandatory PGP communication are now standard, reducing risks for both buyers and sellers. Markets like AlphaBay Reloaded and Incognito use automated dispute resolution and decentralized hosting to minimize downtime and exit scams. DarkMatter is a darknet marketplace built for those who demand both power and discretion. With a futuristic design and advanced encryption protocols, DarkMatter provides a seamless, secure trading environment. Known for its deep vendor network, fast transactions, and stealth-first philosophy, DarkMatter is engineered for users who take anonymity seriously.
- Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries.
- As the network matures, it is expected to play a significant role in the cryptocurrency ecosystem.
- One of the key developments includes ongoing updates to the Lightning Network protocol itself.
- The evolution from IRC to Telegram represents more than just a shift in tools, it signals a transformation in how cybercrime infiltrates daily digital life.
Bitcoin As A Medium Of Exchange
- If the network is ever going to be truly scalable, then it will come in the form of a project like the Lightning network.
- Vendors maintain high standards with discreet shipping methods, including vacuum-sealed packaging and decoy items, reducing interception risks.
- Some indicators can be seen, but it cannot be confirmed with certainty if published transactions were part of a payment channel on the Lightning Network.
- As more businesses and individuals adopt the Lightning Network as a payment protocol, it could lead to the broader adoption of Bitcoin as a currency.
- WeTheNorth is a Canadian market established in 2021 that also serves international users.
This is done by finding a path of payment channels between the sender and the recipient. Lightning is a decentralized network using smart contract functionality in the blockchain to enable instant payments across a network of participants. The Lightning Network can provide a level of anonymity which surpasses that of traditional Bitcoin and Altcoin channels, and its micropayment structure does not hinder potential terrorist financing.
Darknet Markets 2025:
In 1993, “A Cypherpunk’s Manifesto” was published in the Cypherpunk mailing list. It described the importance of privacy in the digital realm and stated that cypherpunks were dedicated to building anonymous systems, including electronic money. 3 When broadcasting a new block, the miner receives both the block reward and the sum of fees users include in their transactions. As such, miners will always include transactions with the highest amount of fees. Multiple inputs could be an indication that funds are derived from multiple users or that the same user funded the channel from multiple sources. Finally, the balance of each counterparty of the channel at the time of creation and closure would also be published.
President Harris Should Buy Bitcoin To Pay Black Americans Reparations
If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop. For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. The dark web itself is not illegal, but it’s largely connected with unscrupulous and illegal operations. It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
There will usually be a centralized server that gathers bitcoin from customers and dispenses them randomly to unlink the customer from the bitcoin they sent. Now that you have a decent idea on why such markets are so important, I’ll do my best to explain why bitcoin is not used there anymore. Bitcoin’s adoption depended on markets like Silk Road to pioneer, and what was special about Silk Road is that it was an almost completely free (as in freedom) market. Free markets are excellent for adoption because they don’t require bureaucracy, permits, regulations or any other form of permission to run.
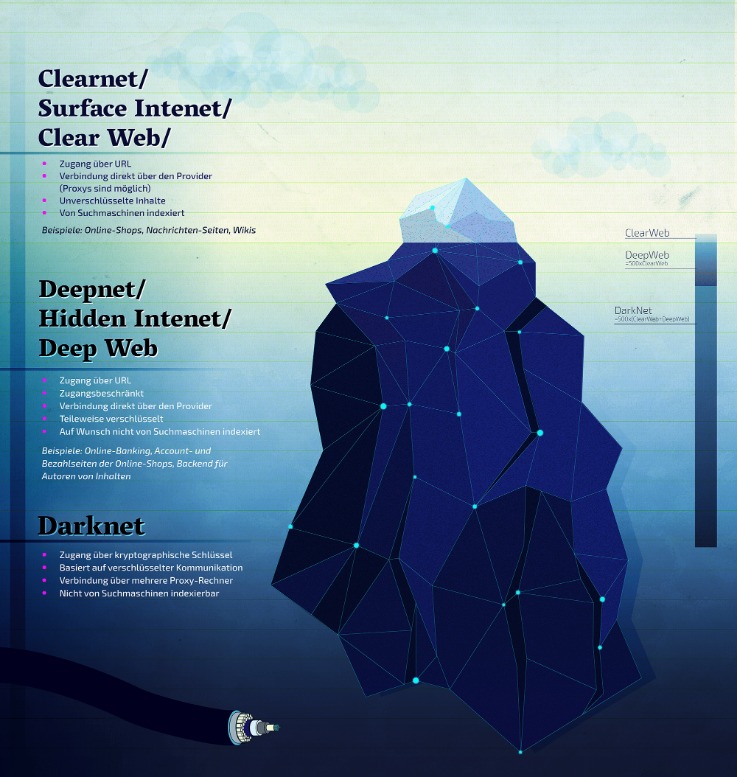
With a refined interface, strict quality standards, and support for multiple cryptocurrencies, Crown positions itself as a platform of excellence and trust. Focused on reliability and discretion, Crown has quickly become a favored destination for darknet users seeking sophistication and stability. Nexus is a darknet marketplace designed to be the central point where trust, technology, and trade intersect. Known for its minimalist design and emphasis on security, Nexus provides a clean, distraction-free environment for users seeking stability and anonymity. With verified vendors, built-in escrow, and lightning-fast performance, Nexus remains a go-to platform for serious darknet users. When opening a channel, participants must commit an amount on the blockchain (a funding transaction).13 Time-based script extensions like CheckSequenceVerify and CheckLockTimeVerify make the penalties possible.
The 2025 landscape emphasizes user experience, with AI-driven recommendation systems matching buyers to reliable vendors. Buyers prioritize markets with real-time tracking and stealth packaging guarantees, which are now common features. The shift toward decentralized platforms has also reduced centralized server vulnerabilities, ensuring longer market lifespans. Reputation algorithms weigh recent transactions more heavily, preventing vendors from artificially inflating scores with old reviews. Markets optimize their escrow systems for Bitcoin, reducing disputes through automated smart contracts.
After the fall of many markets and their vendors because of bitcoin’s privacy flaws and bad operational security, the use of bitcoin was starting to drop. Other cryptocurrencies, like monero, started to emerge on darknet markets because they better fit the use case. Smart contracts are sets of rules that must be followed for transactions to take place. For example, users can attach fees to transactions that are paid to each node it passes through. A smart contract would make sure that fees are only paid after the transaction is completed. The darknet has evolved into a decentralized marketplace where buyers access a wide range of products with fewer barriers than traditional platforms.

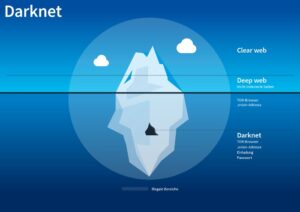
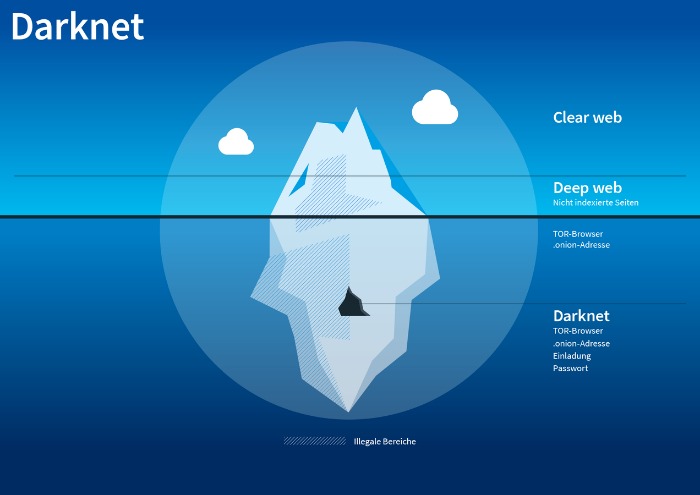
These online marketplaces, hidden from conventional search engines, operate in a secluded layer of the internet accessible only through specialized software like Tor. Here, a wide array of goods and services are exchanged, with a focus on privacy and anonymity. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions.
Every public channel announces its capacity (the total amount of Bitcoin locked in the payment channel). But no information is available for how the capacity is currently distributed in a channel. The technique allows a lightning node to “probe” other nodes in the network in order to find how the liquidity is distributed in their payment channels. When a public payment channel is created, the node sends a `channel_announcement` message to other nodes in the network through the gossip protocol. To avoid spam, the node sending the message must prove that the payment channel exists in the blockchain. This is done by sending the location of the funding transaction along with some other data that can be used by third parties to validate the ownership of the funding transaction.
Decentralized Marketplaces Growth
It’s a market for fake documents, hacking software, and financial fraud services. WeTheNorth has a strong community vibe, with an active forum where users interact and share updates. It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with. And when it comes to paying, the site sticks to Bitcoin (BTC) and Monero (XMR) to keep transactions private. Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not.

In contrast, traditional payment platforms like VISA boasted 6,000 TPS in 2020. Alice does not have an bidirectional payment channel opened with Charlie, but Bob does. If the channel between Alice and Bob is still open, Alice’s Lightning node can route the payment to Charlie through Bob’s node. If Alice and Bob’s payment channel is closed, Alice’s node will try to find another route to Charlie’s node using other connections.