
OSINT professionals use the dark web to gather intelligence from hidden forums, marketplaces, and databases that provide early indicators of cyber threats and leaks. This blog introduces the top 21 dark web resources used by OSINT investigators, cybersecurity analysts, and digital forensics experts. Whether you’re tracking data breaches, uncovering financial fraud, or identifying threat actors, these resources will help enhance your dark web investigation capabilities. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.
Reddit Darknet Market List
With its low 5% vendor fee, secure transactions, and verified sellers, it’s an ideal choice for buyers looking for a trusted marketplace. Finding a trusted dark web marketplace can be difficult, but we offer everything users need for a safe and smooth experience. Chainalysis data shows darknet marketplace revenue dropped post-Hydra seizure in 2022 but recovered to $2 billion in Bitcoin inflows during 2024 Darknet market BTC inflow drop and shift to Monero.
Why We The North Marketplace Stands Out
In 2025, darknet marketplaces primarily accept Monero (XMR) and Bitcoin (BTC). Privacy-focused operators are shifting to Monero due to its default anonymity, compared to Bitcoin’s transparent ledger Darknet markets see BTC inflow drop to $2B. While accessing Darknet Markets themselves is typically not against the law in most places, engaging with illicit goods within them is generally considered a crime. On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues.
Shuttered Markets And Lessons

The dark web is unregulated, which is why it is important to protect yourself while browsing. Start with verified directories like Ahmia or Hidden Wiki, use a secure environment (VM + VPN + Tor), and stick to ethical, research-oriented content only. ZeroBin is an encrypted paste tool on the dark web, often used for sharing messages or files without storing user data. LeakLooker indexes live and historical data leaks found on underground forums, often used to identify early data breach activity. OSINT helps cybersecurity professionals gather publicly available intelligence—often from hard-to-access sources like the dark web—to predict, prevent, and respond to threats.
How To Access The Dark Web

Specialized search engines, directories, and wikis can help users locate the data they’re looking for. The Tor Onion Browser is essential for accessing the dark web, designed for user anonymity. Unlike the regular internet, the dark web doesn’t use standard URLs or search engines. Instead, sites have complex .onion addresses, making them difficult to find without the exact URL. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions. Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions.
Onion Darknet Market
It is now one of the most widely used browsers to access the dark web. The Candle search engine is effective but minimalistic—it gives you only the top ten most relevant results for your search queries. And the search box can’t read certain characters like parentheses or quotation marks, which can be limiting. There are useful resources on the dark web, and you need a dark web search engine to find them. A curated collection of darknet resources for educational purposes, offering insights into darknet frameworks, tools, and security practices.
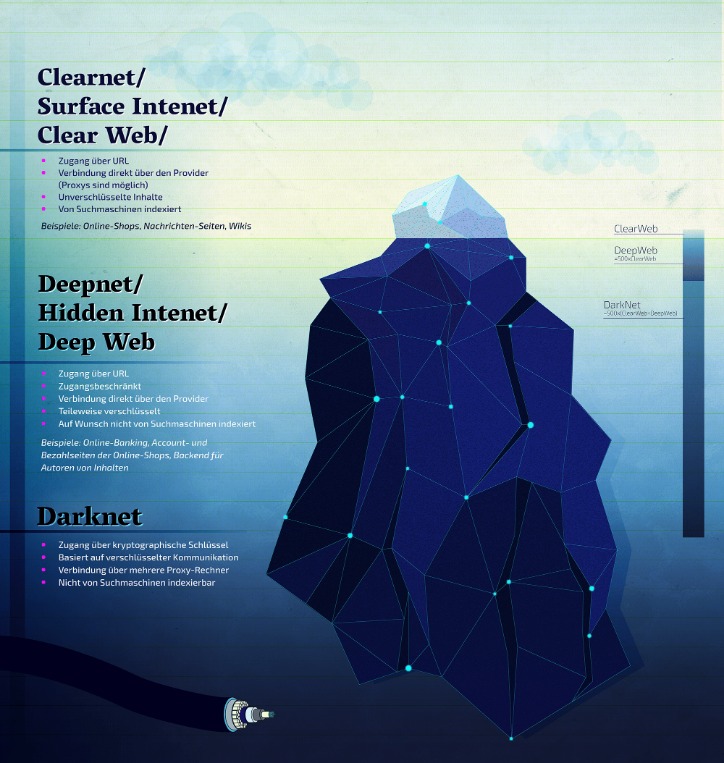
The market claims to provide secure and anonymous commerce services. You can find a lot of goods and services packed with stealth high-level encryption, no JavaScript, and anti-DDoS protection. The dark web is a hidden section of the internet that you cannot reach with common search engines like Bing or Google.
Best Dark Web Sites 2025 – Detailed List
- Torch is one of the oldest and most popular onion search engines on the dark web, serving over 80,000 requests per day.
- It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers.
- The Silk Road was especially known for its role in the online drug trade but was host to other illegal transactions until it was shut down by the Federal Bureau of Investigation in 2013.
- Each server adds a layer of encryption, and this layered system is what lends The Onion Router its name.
- The dark web is designed in such a manner that it hides the identities and locations of its visitors.
- Haystak is often considered one of the deepest search engines for the dark web because it indexes around 1.5 billion dark web pages.
Moreover, sensitive personal documents are made available on the dark web. Some things, like medical records, driver’s licenses, and passport information. The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. The dark web is famous when it comes to hosting as well as spreading explicit and illegal content.
Roundup – Best VPNs For The Dark Web
If for any reason, you decide to visit these hidden corners of the web, ensure you at least study and understand the common traps. Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for.


We recommend you only visit safe dark web links to explore such as The CIA, Facebook, DuckDuckGo, and Torch. Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor.
Can WiFi Owners See Your Internet History?
It’s somewhere Google and Bing don’t index, and you need special tools to get to it. Manual monitoring of the dark web is inefficient and risky due to the sheer volume of data involved. FreshTools, founded in 2019, specializes in selling stolen account credentials and data, particularly webmail, RDPs (Remote Desktop Protocols), and cPanels. The marketplace requires merchants to pay fees to sell their products, helping ensure a certain level of quality control. Here’s a look at the top 10 dark web markets currently dominating this underground space.



