For example, some illicit actors primarily operate off-chain, but move funds on-chain for laundering,” the report noted. In general, the total value in crypto crime excludes revenue from non-crypto-native crime, such as traditional drug trafficking, and other crimes in which crypto may be used as a means of payment or laundering. They sell these files for just a fraction of the original cost on the surface web or even share freely, which makes them tempting for people looking for shortcuts. While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks.
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
- This collaboration helps bridge gaps in jurisdiction and facilitates a more comprehensive approach towards dismantling criminal networks operating on the darknet.
- Darknet markets were one of two categories of crypto crime that saw revenues rise in 2023.
- It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
- In 2019, the FBI started its investigation into Genesis Market and enlisted other government agencies and law enforcement organizations across the world, working towards the market’s closure on April 4, 2023.
- When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
It first became active in early July 2020, with deposit volumes so low it appeared to be less of a darknet market and more a personal operation. However, nearly as soon as Hydra shut down, OMG began seeing high inflows for the first time, more than half of which came from Hydra counterparties. Launched in 2023, STYX focuses on financial crime, providing stolen credit card data, hacked bank accounts and access to various cryptocurrency laundering tools. However, it’s worth noting that markets specializing in other illicit goods also bring in sizable funds. We’ll examine card shop activity in greater detail later in this section. Since this research focused on the darknet drug trade, the collected data was filtered to the drug category based on the product categories provided by the users, resulting in 34,445 valid (not blank) reviews.
According to a recent trend, the dark marketplaces faced a decline in revenue. Chainanalysis, a blockchain analysis firm, conducted research that shows that the revenue decreased from $3.1 billion (2021) to $2 billion (2024). As mentioned earlier, launching a cyberattack doesn’t require any hacking skills.
How Much Is Stolen Data Sold For On Darknet Markets?
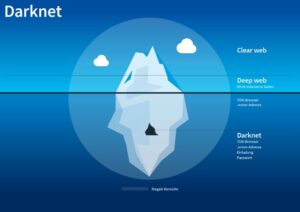
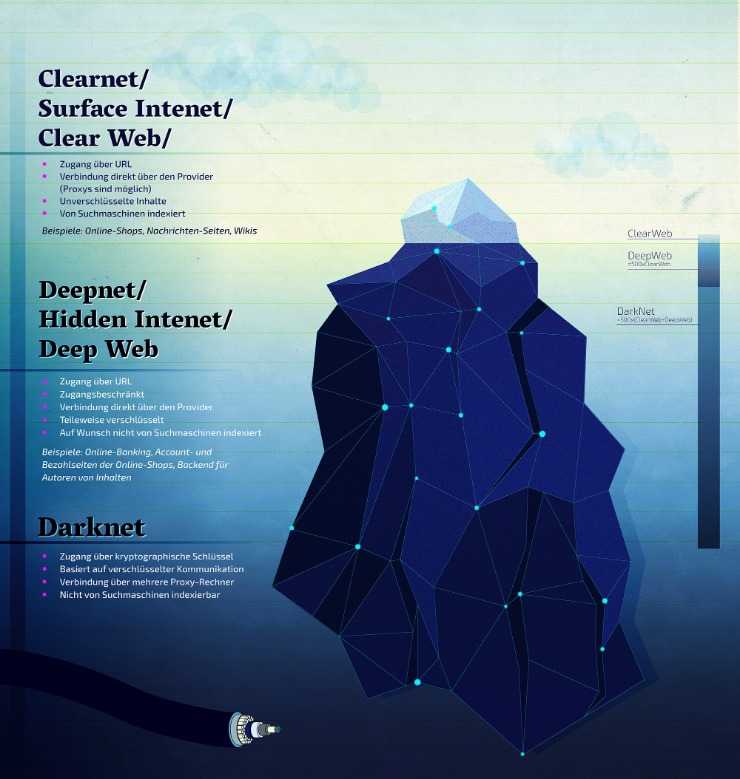
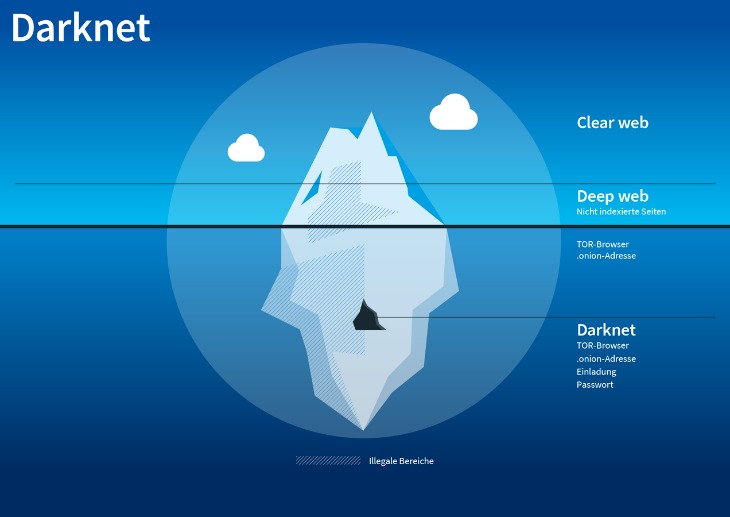
Dark markets, as well as various other services within darknets, are hosted as ‘hidden services’. This means that the servers providing these services are only accessible via Tor and do not have a public IP address or domain name. Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network. This browser enables access to websites with .onion domain extensions, which are specific to the Tor network.
The Takedown Of Garantex: A Notorious Crypto Exchange’s Role In Illicit Finance
Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. Chainalysis also noted that some markets are openly advertising their wares in Russia, with giant 3D billboards (Kraken Market) and QR codes on subway trains (Mega Darknet Market). From underground forums to encrypted communication platforms, you have the power to navigate this landscape with confidence. Operation RapTOR includes law enforcement actions taken by JCODE member agencies, to include ICE HSI; the DEA; FBI; FDA-OCI; IRS-CI; and USPIS; in addition to foreign partners listed below. Local, state, and other federal agencies also contributed to investigations through task force participation and regional partnerships.
How To Protect Your Personal Data Online
Despite increasing criticism of Telegram’s role in cybercrime, the platform only takes limited action against illegal activities. Although channels are occasionally blocked, new groups are usually created within a few hours. In some cases, however, Telegram has begun to assist law enforcement agencies with investigations, particularly in cases of serious criminal activity. Stolen data is traded on illegal marketplaces and used for various criminal activities.
Dangers Of Url Redirection Attacks In Today’s Digital Landscape

Axis Intelligence provides dark web surveillance solutions that help businesses identify leaked credentials, fraud attempts, and malware risks before they escalate. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services. It operates in both French and English and has built a reputation for ease-of-use. You can use a dark web scan tool to tell if your data has landed on the dark web. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. Ever since Silk Road went down, several dark web marketplaces have kept coming and several of them shut down again.
S1 File Frauds Words
If you access illegal content or participate in criminal transactions, you face legal consequences. The legality depends on your activities and your country’s specific laws regarding darknet use. Dark markets include features similar to those found in legitimate e-commerce platforms, such as product listings, user reviews, ratings, and customer support. These features help create a sense of ‘trust’ among users, even in the criminal ecosystem. The concept of darknets emerged as a response to concerns about digital privacy and government surveillance.
The Role Of Cryptocurrencies In Darknet Markets
Dark-web marketplaces operate through encrypted networks, primarily utilizing anonymity-enhancing technologies such as Tor (The Onion Router) and I2P (Invisible Internet Project). These technologies obscure users’ identities and locations by routing their internet traffic through multiple volunteer-operated servers worldwide, making it extremely difficult to trace activities back to individuals. Tor remains the most prevalent method due to its ease of use and robust anonymity features, but the popularity of I2P is steadily growing due to its increased resistance to surveillance and censorship. Although the largest share of stolen funds was robbed from decentralised finance (DeFi) services, centralised services were the most targeted in the second and third quarters, the report said.

Please note that our Terms and Conditions, Privacy Policy, and Disclaimers have been updated. Many operators have since moved to accepting only Monero (XMR),” Chainalysis added. In terms of vendor behavior, the change is largely dominated by wholesale vendors. Meanwhile, retail vendors, who operate on a smaller scale, are holding more of their illicit earnings in personal wallets, delaying conversion to fiat to avoid detection.
Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there. These markets are dangerous anyway and shouldn’t be accessed even if they’ve onion addresses.
When your data is found on the dark web, it means that you’ve been compromised. Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider. The fact that there are no real regulations as well as authorities to monitor transactions, you’re always on your own, and you’re a potential target and victim of a scam or fraud.
Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025. The user interface is similar to that of a regular online marketplace with categories, search functions and a shopping cart system. On the left-hand side is a list covering a wide range of illegal products. These include drugs such as stimulants, cannabis and hashish, opioids, psychedelics and ecstasy, as well as fraud and financial data, including bank accounts, credit card details and other sensitive information.
These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services. The migration of vendors, plus the timing and source of OMG’s initial revenue suggests that Hydra administrators may have been involved with the development of OMG. For instance, Hydra was unique from its competitors in that it offered location-based courier services. Upon account creation, the user would select their location and arrange “dead-drop”-style exchanges from vendor to buyer.