
Navigating the vortex darknet marketplace requires mastery of advanced privacy protection techniques. Users must establish secure Tor browser configurations while implementing encrypted communication tools and robust authentication systems. Successful access to the vortex link requires authenticated vortex onion addresses through properly configured Tor Browser setups. These vortex url gateways utilize military-grade encryption to secure marketplace connectivity.
- Each backup connection maintains equivalent security protocols as the primary marketplace.
- It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals.
- By 2025, darknet markets have diversified, catering to niche demands while maintaining robust operational security.
- This site supports PGP encryption and two-factor authentication features.
- Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
Do I Need A VPN If I Use Tor?

Discover how to safely access dark web marketplace links while ensuring your privacy and security online. Markets like Perico represent the next wave — safer for vendors, harder for law enforcement to trace, and accessible only to privacy-savvy users. For cybersecurity professionals, journalists, and policymakers, understanding how these systems evolve is crucial to monitoring and mitigating the impact of underground economies.
It is one of the most active and up to date markets and always provides new and updated malware and data. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data. Despite its name, the marketplace operates primarily in English and serves a global audience. It has gained a reputation for being a reliable source of high-quality data for cybercriminals. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025.

Secure Drug Trade On Darknet With Market Lists And URLs
Once a buyer makes a payment, it’s usually held in escrow until they receive what they bought. Navigating the kerberos darknet marketplace requires mastery of advanced privacy protection techniques following the kerberos darknet access instructions. Users must complete the kerberos darknet onboarding process while implementing secure communication tools and robust authentication systems. Broken or outdated links can be a major frustration when navigating darknet markets. Many markets go offline without warning leaving users and vendors clueless to what is happening. All darknet markets use escrow this basically means the buyer’s payment is held in escrow until the buyer confirms they’ve received the product which gives a piece of mind to the buyer.
They also include user reviews and ratings, helping newcomers identify trustworthy vendors and avoid scams. User reviews and vendor ratings play a critical role in maintaining trust within these markets. Platforms like Empire Market 3.0 have implemented advanced feedback systems, allowing users to evaluate vendors based on product quality, delivery speed, and communication. This transparency fosters a reliable trading environment, encouraging repeat transactions and long-term relationships between buyers and sellers.
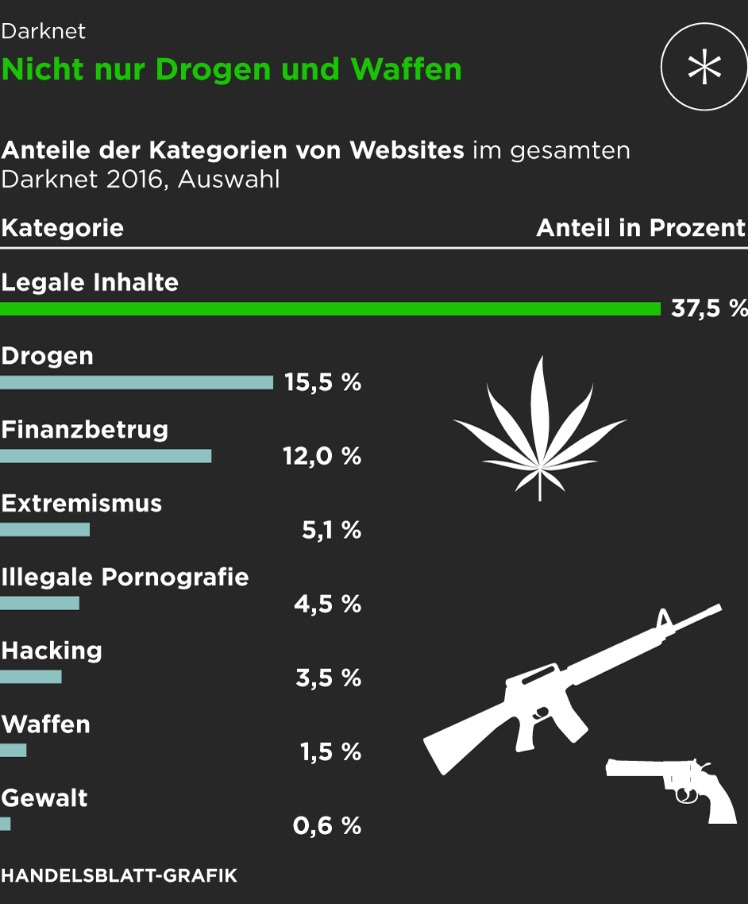
Darknet Marketplaces (DNMs) And How They’re Accessed

However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law. This article reveals the top 10 dark web markets dominating in 2025, their unique characteristics, and the critical implications for enterprise cybersecurity. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites.
Darknet Market Onion Links
For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead.

VPN Alternatives For Securing Remote Network Access
While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. The Invisible Internet Project’s distinctive feature is its ability to use decentralized file storage with the help of the Tahoe-LAFS plugin. In due course, the framework was remodeled and made public as a secure browser.
Tor Browser: Accessing The Darknet
The darknet marketplace landscape in 2025 is dominated by platforms like Nexus and Abacus, which prioritize user experience and transaction security. These markets leverage advanced encryption and decentralized infrastructure to ensure anonymity, making them preferred choices for buyers and sellers. Nexus stands out for its escrow system, which holds funds until delivery is confirmed, reducing fraud risks. Abacus offers a streamlined interface with multi-signature wallets, further enhancing trust.
While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. Plus, there’s a thorough vetting process for new buyers and sellers to keep the community more secure. In a way, it feels more like a private club than an open market, and that’s exactly how the operators want it. To expand their reach, some marketplaces established parallel channels on Telegram.
Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. The dark web contains content that’s only accessible through networks like Tor. Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous.
They’re tightening security and carefully screening anyone who wants to join. This vetting process helps keep the community “clean” from spies, law enforcement, or anyone who might pose a risk. But these efforts of law enforcement don’t go in vain; hackers and criminals lose trust if a website or marketplace goes down.
This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. Onion links have no regular domain names registered under the domain name registry. Instead, they are designed using a cryptographic key and can be accessed only through software like the Tor browser.
Where To Find Darknet Market Links
People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content.
As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. It became the blueprint for other dark web marketplaces that tried to take its place. Ulbricht faced several serious charges, including distributing illegal drugs, running a criminal enterprise, hacking, trafficking fake IDs, and money laundering.



