
As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others. Then, simply click the operating system that you are using and download the file. While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. It’s impossible to access the dark web with a regular browser like Chrome or Safari. That means that when Tor is compromised, or perhaps there’s a new vulnerability exploit in the Tor network, a VPN will still protect your privacy. The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you.
Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny. The US Supreme Court has indicated that even casual browsing could lead to legal consequences.

So, next time you’re tempted to explore the dark web, remember the importance of staying safe and secure with the right tools at your disposal. Utilizing The Onion Router (Tor) network, these sites encrypt user data, providing layers of protection much like an onion. Users access these sites via the Tor Browser, which conceals their identity and location. Scammers prowl the dark net, launching fake storefronts that vanish overnight, often with their victims’ money. In 2017, a global police operation brought down AlphaBay, the dark web’s largest illegal marketplace, shaking the underground economy.
Exposure To Malware And Scams
Since then, many copycat markets have tried to replace it, but not all of them have lasted. Finally, product variety significantly influences marketplace choice. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users.
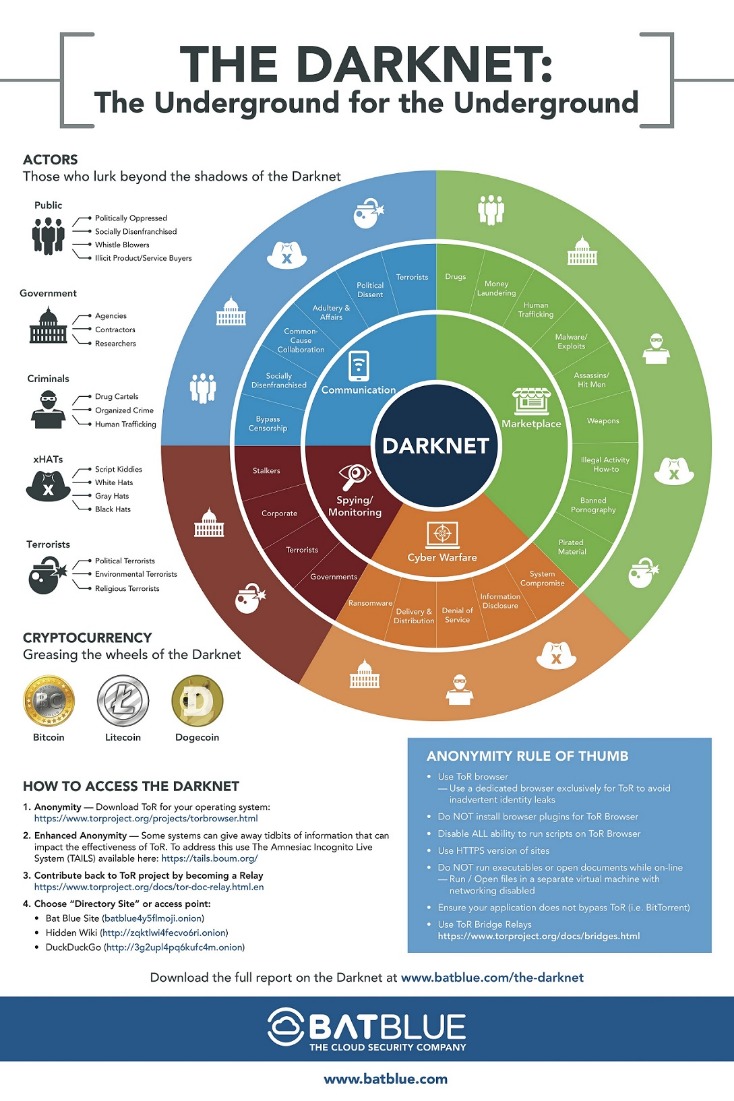
- A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous.
- It offers impressive features, including PGP-signed addresses, payment via Monera, sticky and featured listings, and auto shops.
- When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
- A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.
- And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever.
But lurking beneath lies the expansive, mysterious “deep web” or“dark net” – the gigantic submerged part that remains invisible to standard searches. When your data is found on the dark web, it means that you’ve been compromised. Therefore, you need to start by changing your passwords, and you need to notify your credit card or bank provider. STYX market features a robust verification process, making it look more exclusive. In fact, they have a Telegram channel to offer users with live updates. The platform supports Monero (XMR), Bitcoin (BTC), and several others to hide identities.
Tor2door Market
That way, a business can stay ahead of the game and respond swiftly to any possible threat, while protecting its reputation and customers. Tor offers secure and encrypted access to the dark web forums, ensuring that the user’s IP address is hidden and difficult to trace. Therefore, cybercriminals use these forums because they offer assured anonymity and security. Moreover, stolen credit card markets such as BrainClub and BidenCash used to advertise on XSS. Its regular users claim that its longevity and popularity were a result of its overseas management and a strong admin handling of the operational security (OPSEC).
Torzon Market
Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic. The “Hidden Wiki” (which can be accessed in a normal browser) offers a large collection of dark web links, but be careful, as many of those links are to dangerous websites. In 2002 the dark web began to grow significantly when researchers backed by the U.S. The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web.
- Finding the correctly represented URL for a particular domain in the first instance can be a challenge.
- Cybercriminals want to carry out their illegal activities without detection by law enforcement agencies and other authorities.
- Begin your journey by solving a simple visual captcha — align the grid, prove you’re not a bot.
- Simply accessing the dark web and using the Tor browser may already raise government suspicion.
Tips For Safe Exploration

The dark web addresses are a randomly-scrambled sequence that generates URLs, mostly hard to remember ones. For example, the URL of Silk Road is rather unintelligible and may look something like “gan4arvj452janndj4a76.onion”. So, that means that the number of pages increased by over 100 trillion in just over three years.
Shifts In User Behavior And Marketplace Structures
For instance, the Ashley Madison data dump was posted to a site only accessible to Tor users. As I’ve mentioned, the dark web isn’t just a place of eternal torment, teeming with drug dealers, human traffickers, and a hitman. It’s also used by journalists, advocacy group members, and political refugees in hiding. Reuters, Fox, NBC, CNN – all of them keep open dark web channels to receive anonymous tips from whistleblowers. So, it’s only natural to find ways to keep in touch with your darknet buddies and/or customers.
The Dark Web: Risks And The Role Of Standards
However, it is important to note that not all of this content is legal. When you open your default browser, Freenet will be ready and running through its web-based interface. Note you should use a separate browser than the one you normally use to help ensure anonymity. For built-in Tor over VPN functionality, NordVPN operates specialized servers that automatically route you through the Tor network. You don’t even need to use Tor Browser, but keep in mind other browsers can still pass identifying information through the network. Alternatively, there’s IPVanish who claim to be the world’s number one VPN for Tor and comes highly recommended, you can save 60% on the annual plan here.
Do I Need A VPN If I Use Tor?
Of course, not all the popular and widely-used dark web sites and things like marketplaces on the dark net are illegal. Some use them due to privacy concerns, such as journalists talking to informants or whistleblowers, while others may simply want to protect their confidential information from observation or tracking. Nevertheless, most people on the internet do not need to communicate or venture into the dark web. The dark web is a hidden section of the internet that you cannot reach with common search engines like Bing or Google.
How Can I Enhance My Privacy While Accessing The Dark Web?
If you take a quick look through darknet marketplaces, you’ll instantly notice an overwhelming supply of pirated content. We’re talking about even early access to unreleased music, leaked TV episodes, concert footage, and even popular video games before they officially drop. One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive. They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace.
Common Scams And Fraudulent Activities On Darknet Markets
Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. Darknet marketplaces may look like regular online stores, but using or even browsing them comes with serious risks. From identity theft to law enforcement surveillance, the dangers are real — and often underestimated. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there. The first ever DNM — called Silk Road — was started in 2011 by U.S. citizen Ross Ulbricht.
The ability to seamlessly communicate with vendors via secure messaging systems also greatly improves overall user experience. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes. Platforms known for consistently resolving issues and eliminating fraudulent vendors quickly gain credibility and user loyalty. It comprises several forums, web platforms, and marketplaces usually hosted on encrypted networks and often run by independent groups or individuals.



