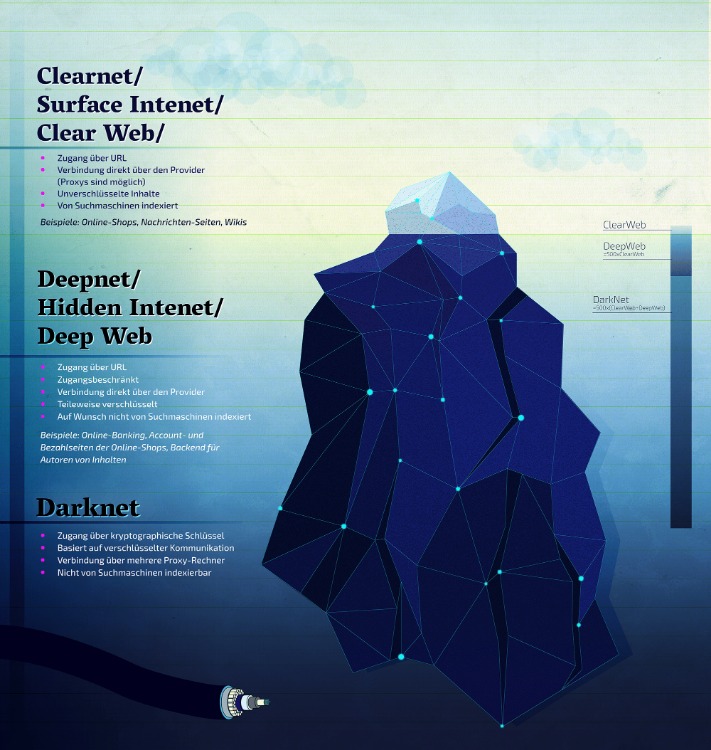
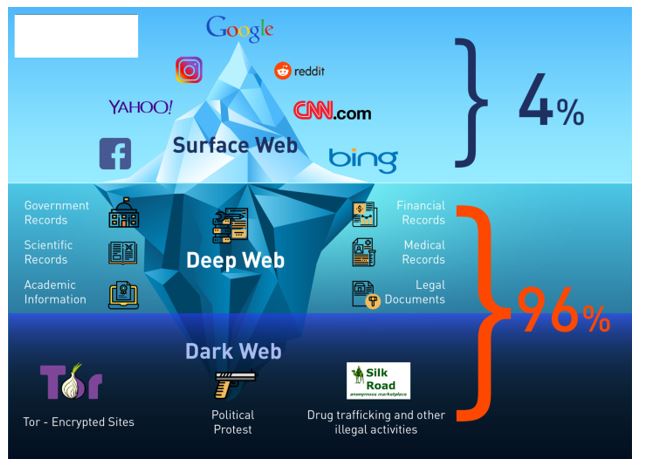
The deep web consists of anything online not indexed by standard search engines, such as personal email accounts, online banking, private databases, and subscription-only content. While the deep web is hidden from public view, it is not inherently malicious and is used daily by individuals and organizations to protect sensitive information. However, it is worth delving deeper into the unique features of each search engine to understand their performance in more detail.
Web Address:-
- It includes all the essential productivity software, including MS Word and an email client.
- Haystak also has a paid version which offers a number of additional features such as searching using regular expressions, browsing now-defunct onion sites, and accessing their API.
- To access the dark web, you need to use a combination of tools (like Tor + VPN + a dark web search engine) explicitly designed to find content on the dark web.
- However, The Wayback Machine allows website owners to block their sites from being archived, while archive.today does not.
- Install Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online.
Using the Tor Browser with a VPN is a safer and more secure option, as it provides end-to-end encryption and better privacy protection. OnionLand offers a clean design with a simple user interface that includes search suggestions. The search engine allows you to look for old V2 onion addresses, images, and content on I2P.
Are Dark Web Search Engines Useful For Cybersecurity Research, And How?

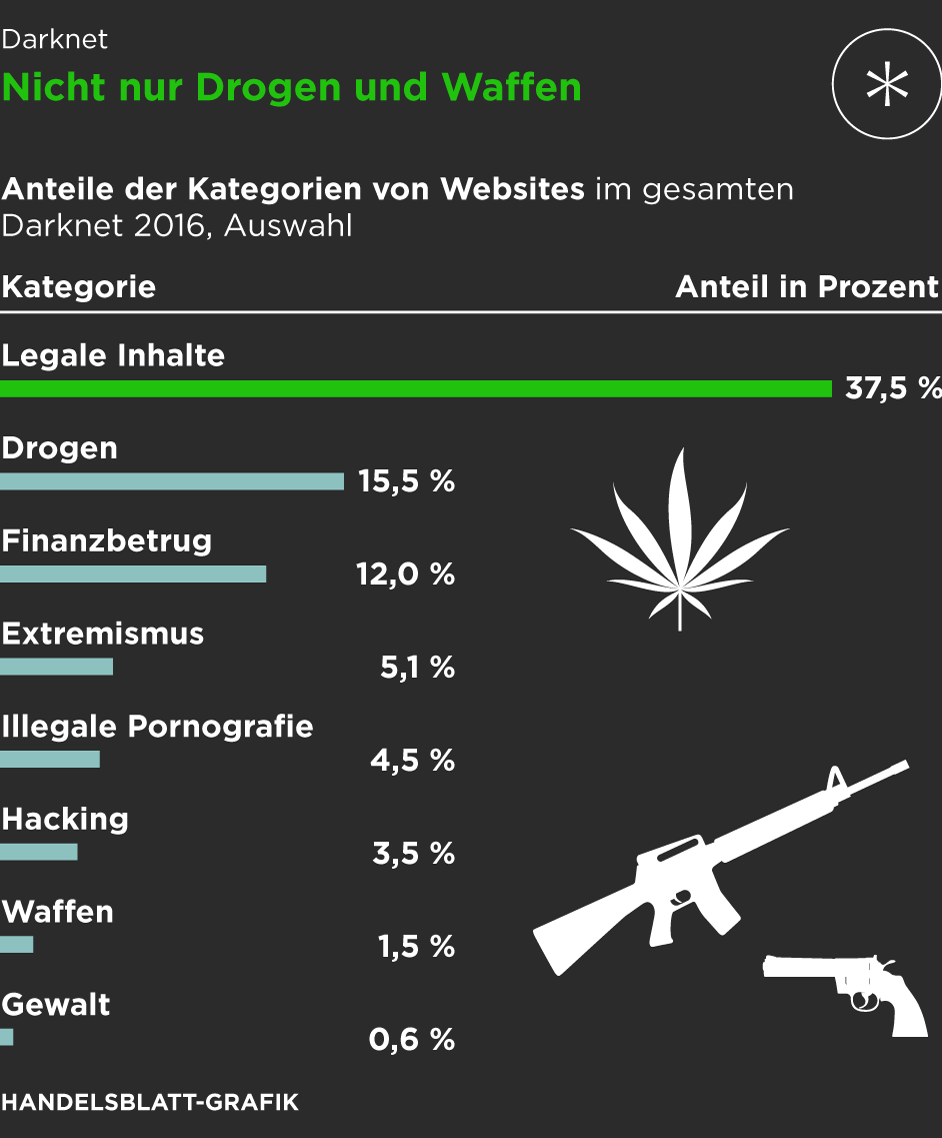
Even on the clearnet, the results you’ll see are that of .onion domains. Most other clearnet domains for similar services either just redirect, or share their own onion alternative. Out of the 10 sites shown on the first page for each search, there mostly are only 2-3 unique websites. Staying anonymous is needed not only by whistleblowers but also by credit card scammers, drug dealers, etc. While you’ve probably heard of all the criminal activities that take place, one of the most significant benefits of using a Deep Web Browser is being able to browse the internet anonymously.

But the lack of filtering is a constant headache; I’ve learned to cross-check every link via directories or forums and keep my antivirus on high alert. The outdated UI feels like a relic, but its speed and availability make up for it. Its billion-page index is a treasure trove for broad searches, and I’ve uncovered gems like obscure tech blogs or retro V2 sites that other engines miss. The CIA is contactable on the dark web, providing a completely anonymous way to get in touch with them. However, if you’re communicating with state intelligence agencies, you should use Tor alongside a VPN for maximum privacy.
For this reason, you must watch out and avoid opening anything that looks suspicious to you. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc. One option is to try DuckDuckGo’s .onion version, which is great for privacy. Other options include Ahmia and NotEvil, which focus on listing .onion links. It will offer you an additional layer of encryption to access the deep parts of the internet.
Dark Web Search Engines
Using a virtual private network (VPN) masks your real IP by routing your internet traffic through a secure server, making it appear as though you’re browsing from a different location. A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access. It’s specifically designed for privacy, routing your connection through the Tor network to hide your IP address and encrypt your traffic. Built-in features like script blocking and anti-tracking ensure a safer browsing experience. While they make accessing Tor-hidden websites easier without the Tor browser, they can compromise your privacy and security by acting as intermediaries that might expose your data.
How Onion Search Engines Work
This period saw dark web search engines diversify, catering to varied user needs—scale, safety, and accuracy. Haystak (2018) introduced a freemium model, catering to power users with a premium tier offering deep indexing (~2 billion pages), regex searches, and historical archives. Its focus on V3 .onion addresses aligned with Tor’s security upgrades, but its unfiltered results required robust user caution. Users relied on handwritten lists or email chains to share .onion links, with no centralized indexing. The lack of search tools made the dark web a fragmented, insider-driven space, inaccessible to most. NotEvil, a successor to TorSearch, is a dark web search engine launched in the mid-2010s, designed to index .onion sites with a focus on privacy and safety.
And most importantly, be patient as you’ve to sort through a lot of useless results. These search engines work best if you already know what site you’re looking for, not for general browsing. Though they have their limitations, most of the time you’ll see irrelevant or spammy links for your search results.
Email Services
The network is comprised of thousands of volunteer-run servers known as Tor relays. Such anonymous networks are the focus of attention not only of ordinary people fleeing censorship but also of criminal cartels. Many different applications are used to hide the users’ identities and ensure the security of the data they transmit on the internet. While some of these applications only work as a proxy server, there are also versions that can be installed as stand-alone software or an operating system. Some applications have their own network infrastructure, while others use the network infrastructure of other applications. The search engine enables registration, which allows registered users to request the site to add new onion sites they would like to be indexed.
Monitor Network Activity
With this in mind, finding verified links is crucial for avoiding threats on the dark web. Torlinks (2019) and The Hidden Wiki evolved with V3 .onion support, reinforcing directories’ role in structured navigation. By 2025, dark web search engines balance accessibility, security, and scale, reflecting the dark web’s maturation into a complex, multifaceted ecosystem.
- Always prioritize ethical practices, and ensure that your dark web investigations are conducted with full legal compliance and operational security.
- If your team can find stolen credentials as soon as they appear on the dark web, you can be proactive about preventing an attack with specialized dark web search engines.
- If you’re curious about how to explore .onion sites safely and effectively, this guide will walk you step-by-step through the process.
- The Directory of Open Access Journals is a deep internet search engine that provides access to academic papers.
- Dark web engines like NotEvil index these domains exclusively, allowing keyword-based discovery of sites that surface engines can’t reach.
The most common tool is the Tor browser, sometimes used with a VPN for additional anonymity and protection. Always prioritize ethical practices, and ensure that your dark web investigations are conducted with full legal compliance and operational security. OSINT professionals must venture where conventional tools can’t reach—and the dark web is one such frontier. It also has a “more results from site name” link with each duplicate group. Meaning, if you wish to see more results for your keyword but from that specific website, it’s possible as well.
These domain names are not registered with a central authority but are instead derived from cryptographic keys. Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins.

When used with a dedicated private browser, DuckDuckGo can be a powerful search engine and a potent privacy tool. No, conventional search engines like Google cannot be used to access the dark web. As a result, Torch is often considered one of the leading dark web search engines. Haystack doesn’t track or store your search queries or personal data, which is critical to maintaining anonymity on the dark web. Haystak boasts an impressive index of over 1.5 billion pages from more than 260,000 websites on the dark web.
Is It Illegal To Visit Websites On The Dark Web?
Whether you’re a journalist, researcher, cybersecurity professional, or just curious, these platforms can help you navigate the deep corners of the internet — carefully and securely. Haystack just might have the most indexed dark website on any dark web search engine at over 1.5 billion indexed pages. It runs on a freemium model, however, so you will have to pony up some cash to go ad-free and for features like access to historical versions of websites. Like DuckDuckGo, Haystack is a privacy-friendly choice, promising not to track your data or compromise your privacy for profit. The dark web is a part of the internet that isn’t accessible with regular browsers or search engines like Google and Bing. To explore it, you need special tools like the Tor browser (short for The Onion Router) and search engines designed specifically for the dark web.
And it also operates without ads, which can be particularly helpful when navigating the dark web. The dark web is an unknown hidden part of the internet that cannot be accessed with default browsers. It can be accessed using specialized software and allows users to hide. Some of the raison d’être of the dark web is to provide privacy and anonymity, making it a valuable tool for people whose access to information is restricted. Some people or organizations even use the dark web as a tool to protect their data. As a result, the purpose of the dark web varies from person to person.