Sharing a lot of similarities with Exploit, the XSS cybercrime forum also attracts a mixture of threat...
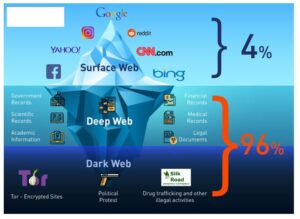
It had a surface web mirror alongside an onion site that users accessed using the Tor browser....
They took it, got it into airplane mode right away (so that I couldn’t remote erase it...
“You’re seeing the evolution of a coordinated law enforcement effort,” the director of Europol’s European Cybercrime Centre...
This, combined with the use of onion addresses, ensures that users can access these platforms without exposing...
They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails....
That means you may violate copyright laws while downloading books, so use a VPN to protect yourself...
For most people and use cases, using only a VPN will offer sufficient privacy with much faster...
A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra...
One of Daniel’s impressive features was the built-in functionality that showed whether a particular dark website is...