In contrast to the other types of sellers, the median income of U2U-only sellers increases after operation Bayonet. Moreover, we observe a trend of increase in their median income relative to the value before operation Bayonet—an increase of almost six times by the end of the period of observation (see Supplementary Information S4). Further supporting this interpretation, we observe that the trading volume of the U2U network increases after Bayonet, while the trading volume of markets decreases (see Supplementary Information Section S4). DEXs facilitate anonymous crypto-to-crypto swaps without identity verification, leveraging cross-chain bridges and privacy tools to obfuscate transactions. Some P2P enable off-ramping via cash and prepaid vouchers, bypassing AML compliance under claims of mere facilitation.
With 44,737 shuffles using Cashshuffle to-date and close to $100 million transactions shuffled, the protocol has gathered a lot of traction. Additionally, at 94,574 accounts on Local.Bitcoin.com since the peer-to-peer platform’s launch, data indicates there’s significant interest in trading privately. There have also been 2,250 fusions so far using the Cashfusion protocol since November 28, 2019, and there’s been 10,103 BCH fused to-date ($4.5 million). Its extra layer of encryption has afforded protection to activists in oppressive regimes fighting for civil rights and free speech. SecureDrop has been used by journalists to communicate with anonymous sources, and encrypted email service ProtonMail developed by MIT and CERN is another well-known denizen of the darknet. The CIA has its own ‘onion site’ on the Tor network, encouraging foreign intelligence sources to share secrets without fear of detection or reprisal.
Implications For Security Leaders
The number of multisellers steeply decreases after operation Bayonet but they still sustain high incomes. Throughout the whole period of observation, the dominant category of buyers is market-U2U buyers followed by market-only buyers, representing on average 52% and 42% of all buyers, respectively. The U2U-only category is comparatively small, representing only 6% of all buyers on average. The number of market-U2U and market-only buyers also drops as a consequence of operation Bayonet.
Historic First: US Government Posts GDP Data On Bitcoin Blockchain
Interestingly, the S2S network shows an intermediate level of resilience, which suggests that the S2S network might play the role of a supply chain network on the dark web. Furthermore, after a shock, the activity of buyers is resumed almost immediately, while the activity of sellers recovers more slowly. These different regimes suggest that the ecosystem’s resilience is mainly supported by the high demand of buyers rather than the response of the sellers. In order to investigate the role of direct transactions between market participants, we now analyse the evolution of the S2S network, i.e., the network of the U2U transactions involving only sellers.
Bitcoin Has Lost Steam But Criminals Still Love It
We show that these users play a crucial role in the connectivity of the ecosystem because they act as connectors between markets. Analogously, we identify and characterise ‘multisellers’ (i.e., multihomers that are sellers) and ‘multibuyers’ (i.e., multihomers that are buyers). Furthermore, we analyse the seller-to-seller (S2S) network, i.e., the network composed only of transactions among sellers, which can be regarded as a supply chain network of illicit goods and services. We highlight that these networks exhibit different resilience regimes in the presence of external shocks, the ecosystem’s resilience being mostly guaranteed by the network of buyers rather than sellers.
Emergence And Structure Of Decentralised Trade Networks Around Dark Web Marketplaces
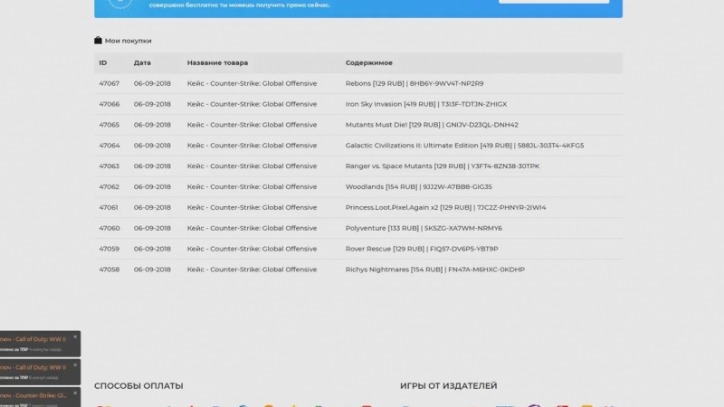
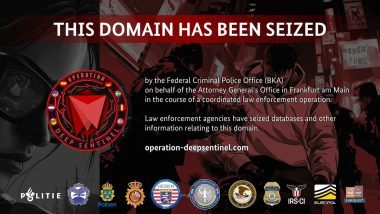
“After major exchanges delisted XMR, we observed a significant shift back to Bitcoin. The reduced accessibility of Monero forced users to rely on a more liquid and widely accepted asset,” Jardine stated in an interview with CoinDesk. Archetyp Market was dismantled in June 2025 during Operation Deep Sentinel in a coordinated raid across six countries.
The Future Of Privacy Cryptocurrencies And Their Role In The Darknet

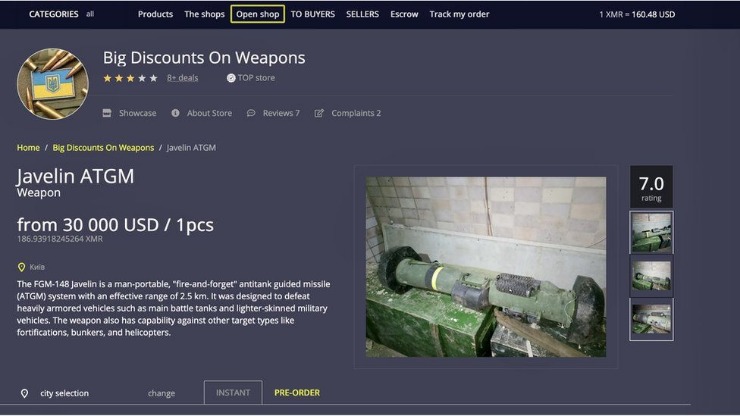
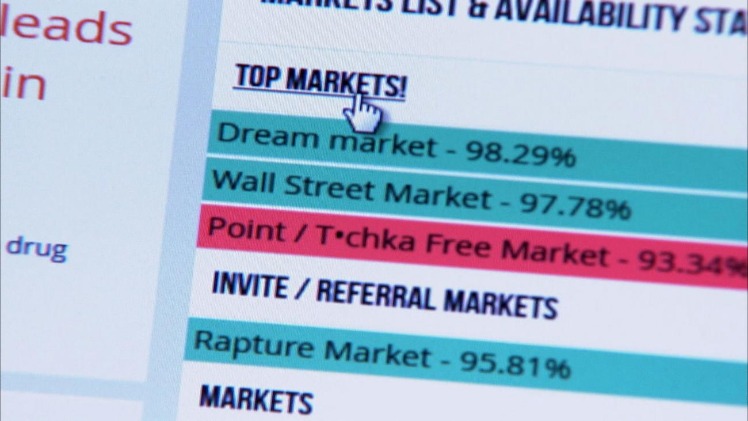
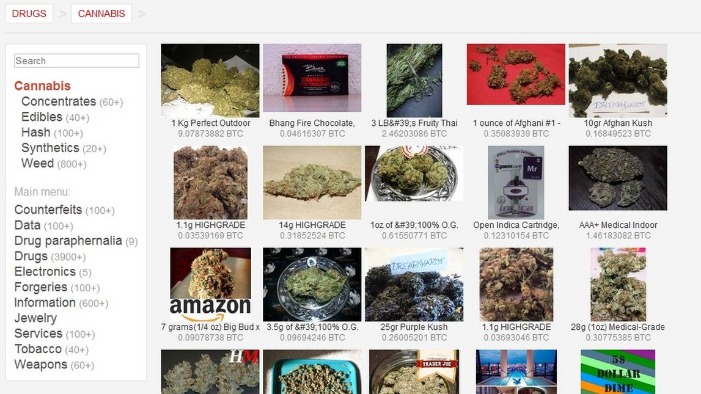
Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users. Its focus on financial fraud and high-value transactions has attracted a dedicated user base, contributing to its growing reputation and market value. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem. To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself.
The Dark Web Privacy Dilemma: Linguistic Diversity, Talkativeness, And User Engagement On The Cryptomarket Forums
- A recent high-profile case involved the shutdown of the Nemesis online marketplace.
- CoinJoins of all sorts, stealth address solutions like silent payments and BIP47, and encouraging users to run their own node and use non-custodial and open-source software where they can.
- The reason is that the operational structure of DWMs inherently hides the seller–buyer link, as all transactions are made through the marketplace.
- It is one of the most active and up to date markets and always provides new and updated malware and data.
- TRM provides blockchain intelligence to help financial institutions, cryptocurrency businesses, and public agencies detect, investigate, and manage crypto-related fraud and financial crime.
Other general statistics about our dataset can be found in the Section S3. Overall, our study provides a first step towards the understanding of how users of DWMs collectively behave outside organised marketplaces. Our research details a thriving underground economy and illicit supply chain enabled by darknet markets. As long as data is routinely stolen, there are likely to be marketplaces for the stolen information. The stolen data supply chain begins with producers—hackers who exploit vulnerable systems and steal sensitive information such as credit card numbers, bank account information, and Social Security numbers. Next, the stolen data is advertised by wholesalers and distributors who sell the data.
Additionally, where non-compliant cash out points are facilitating the movement of illicit funds from DNMs, regulators and law enforcement may take action to disrupt activity at the cash out point itself. For example, concurrent with the takedown of Hydra was the sanctioning of Garantex, the Moscow-based exchange that made multiple transactions with Hydra-linked addresses. The dark net is famous for being a hub of black market websites for buying and selling products and services. If you purchase something from such shops and make payment through conventional payment methods like your bank transfer, credit/debit card, or PayPal, you can be caught easily and face legal consequences.
We Provide Live And Historic Crypto Charts For Free
This raises questions about how cryptocurrencies can coexist with an increasingly strict regulatory environment without losing their appeal to certain sectors, legitimate or not. The evolution of financial privacy,its relationship with transparency,and the balance between control and freedom will be key to understanding the future of dark networks and the cryptocurrencies that drive them. The recent exclusion of Monero by large exchanges has promoted a return to Bitcoin in Darknet markets, demonstrating how regulations directly impact privacy cryptocurrencies. Despite restrictions, the demand for anonymity and privacy persists, and developer communities continue to seek innovative solutions to maintain these values. Despite current difficulties, projects like Monero remain active due to committed communities and continuous technical growth aimed at improving privacy and security. Privacy cryptocurrencies are not only for illicit purposes but also represent a paradigm for protecting financial privacy in an increasingly monitored world.
Is It Illegal To Access The Dark Web?
Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. Bitcoin stealth addresses, prominently BIP47, introduced a way to have a stealth, reusable address that only discloses the real address of the user when a notification transaction was made. Now that you have a decent idea on why such markets are so important, I’ll do my best to explain why bitcoin is not used there anymore.
IREN Posts First Full-Year Profit On AI Cloud Growth, Mining Expansion; Shares Climb
- Our research shows that, like most legal commodities, stolen data products flow through a supply chain consisting of producers, wholesalers, and consumers.
- Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely.
- Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website.
- First, though, there are several interesting high points worth highlighting in Chainalysis’ report regarding the entirety of illicit activity that cryptocurrencies enabled.
- It has grown to become the largest darknet market in operation, receiving $1.4 billion in bitcoin payments in 2020.
- However, trading behaviour in DWM closely resembles what is observed on regulated online platforms despite their significant differences in operational and legal nature14.
The more people that use bitcoin privately, the better privacy everyone gets, and the more likely it is that bitcoin will emerge again as the prominent currency of the darknet markets, and consequently of other markets too. Bitcoin’s accessibility allows clandestine markets to conduct fluid and fast operations, which privacy tokens, affected by legal restrictions, cannot currently guarantee. While Monero’s inherent privacy is limited by exchange exclusions, Bitcoin maintains an open ecosystem where buyers and vendors can exchange illicit goods with relative ease, albeit with less anonymity.