In the summer of 2017, a team of cyber cops from three countries successfully shut down AlphaBay, the dark web’s largest source of contraband, sending shudders throughout the network. Some alleged services like the professional “hitmen” may just be scams designed to profit from willing customers. Reports have suggested the dark web offers many illegal services, from paid assassinations to trafficking for sex and weapons. Malicious software — i.e. malware — is fully alive all across the dark web. It is often offered in some portals to give threat actors the tools for cyberattacks.
Google Warns About 97 Zero-Day Vulnerabilities Exploited In 2024
Using a VPN in conjunction with the Tor Browser is an excellent way to keep your online travels secure and private. A VPN’s ability to hide your Tor usage from your ISP and from government authorities makes for a valuable addition to your online privacy arsenal. When you install the Tor Browser, it comes preconfigured with the most secure privacy settings. That means Javascript is disabled, extensions are disabled, and the browser is configured to warn you if an attempt is made to download a file and open it in another application. Each of these nodes removes or “peels” away a single layer, which uncovers the data’s next node destination. When the final layer of the “onion” is reached and decrypted, the message arrives at its destination.
Is Tor Browser Safe To Use?
This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing). Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes. Some consider VPN over Tor more secure because it maintains anonymity throughout the entire process (assuming you pay for your VPN anonymously). Although the official Tor Project advises against VPN over Tor, both methods are superior to not using a VPN at all. You can now safely browse dark web websites and hidden wikis, but if you plan to do anything more than that, you’ll need to take several precautions.
Can I Be Traced, Tracked, Or Hacked If I Use Tor?
The dark web is a hidden part of the web that carries several illegal activities, including drug and weapon dealing, pornography, private data, and more. But, this isn’t only about bad things; you can also get useful information. The Dark Web remains a shrouded corner of the internet—an enigmatic space where privacy, free speech, criminality, and censorship resistance intersect. As digital landscapes evolve, so do the methods of accessing hidden content and maintaining anonymity.
How To Watch The Google IO 2025 Keynote
This guide will teach you how to install the Tor Browser in Windows easily so you can access the Dark Web or browse the web anonymously. The same general process applies to other operating systems, as Tor is also available for Mac and Linux. By keeping an eye on these alternative platforms and trends, you gain a deeper understanding of how privacy, anonymity, and underground markets adapt to new technologies and challenges. As digital ecosystems morph, staying informed and agile will help you make the most of evolving privacy tools—or avoid stepping into ever-more complex traps.
Step 2: Download Tor Browser
Since the dark web is hidden from the surface web, these dark web search engines allow users to explore the concealed part of the Internet. All websites on the open web can be accessed through standard web browsers such as Firefox, Internet Explorer, and Google Chrome. These publicly available websites are labeled with registry operators such as “.com” and “.org.” The websites are easily found because search engines can index the web through visible links. This process is called “crawling,” where the crawlers follow links to different websites and index them for future reference. Unlike Tor, which lets you access both the regular web and .onion sites, I2P is more focused on its own internal ecosystem. It offers access to unique websites known as “eepsites” (which end in .i2p) and supports anonymous messaging services.
GNUnet – Network-Level Privacy
Even if you never make a purchase, you could be watched and incriminate yourself for other activities later in life. The dark web, however, is a very concealed portion of the deep web that few will ever interact with or even see. In other words, the deep web covers everything under the surface that’s still accessible with the right software, including the dark web. The deep web rests below the surface and accounts for approximately 90% of all websites. This would be the part of an iceberg beneath the water, much larger than the surface web.

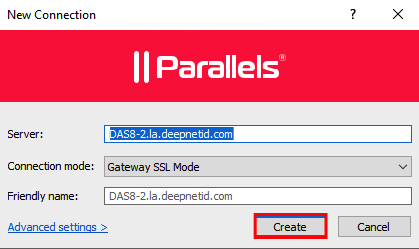
As opposed to the previous situation, here, you’re first connecting to Tor and then the VPN. Not many providers support this, so a manual and sometimes tedious configuration is needed. NordVPN and many other providers offer Tor Over VPN or Onion Over VPN – whatever you want to call it. Regardless of its nomenclature, this is by far the safest option you can go for. It works by first using a VPN and connecting to Tor afterward, hence its name. From here, you can visit any Onion website and enjoy the dark web safely and without worries of ISP tracking and surveillance.

- The dark web may be safe in some cases—think legitimate content—and not in others.
- Launch the VPN app and sign in with your username and password, which are the login credentials you established in the subscription stage.
- This irreversible process highlights the importance of taking preventive measures by utilizing a service that monitors your data for potential breaches.
- A VPN keeps all of your online activities – including your web browsing, online gaming, streaming, and file-sharing – undercover and safe from being tracked or recorded.
- Freebie VPNs will track their users’ online usage, as they make money by selling this tracking info to advertisers and other nosy parties.
And once you’re inside, one wrong click on a fake .onion site can expose your identity or infect your device with malware. Unlike typical web browsers, Tor Browser uses onion routing, which encrypts and routes traffic through multiple servers around the world to hide your IP address and provide private browsing. In addition, all domains on the Tor network end with the top-level domain .onion (instead of .com). The many layers of an onion represent the multiple layers of encryption in the Tor network. Most of the deep web is used for specific needs like researching data and accessing personal accounts.
The darknet is a private place where nobody can intercept, monitor, and steal anything online from you. Because it’s the most secure option when it comes to anonymous browsing. It protects your identity, hides your location, and gives you access to .onion sites that are not available on the regular web. That’s why it’s the go-to choice for journalists, activists… and, of course, curious internet users. If you’re researching how to access the deep web, you’ll definitely come across Tor. And that’s no coincidence—it’s the most popular and trusted browser for exploring this hidden part of the internet.
Tor is a network of volunteer relays through which the user’s internet connection is routed. The connection is encrypted, and all the traffic bounces between relays worldwide, making the user anonymous. Don’t download anything unless you’re absolutely sure it’s safe.

The compromised Tor exploit might trace back to you, but then again, your VPN will lead it somewhere else – which makes it impossible to be traced back to you. It’s not a secret that ISPs (Internet Service Providers) and the FBI are tracking Tor users. Obviously not all Tor users, but you never know whether someone might be looking into you.
At DeepWeb, our goal is to keep you informed about the latest developments in the darknet sphere. From technological advancements to security updates, our expert articles and news updates are designed to keep you at the forefront of industry knowledge. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution.