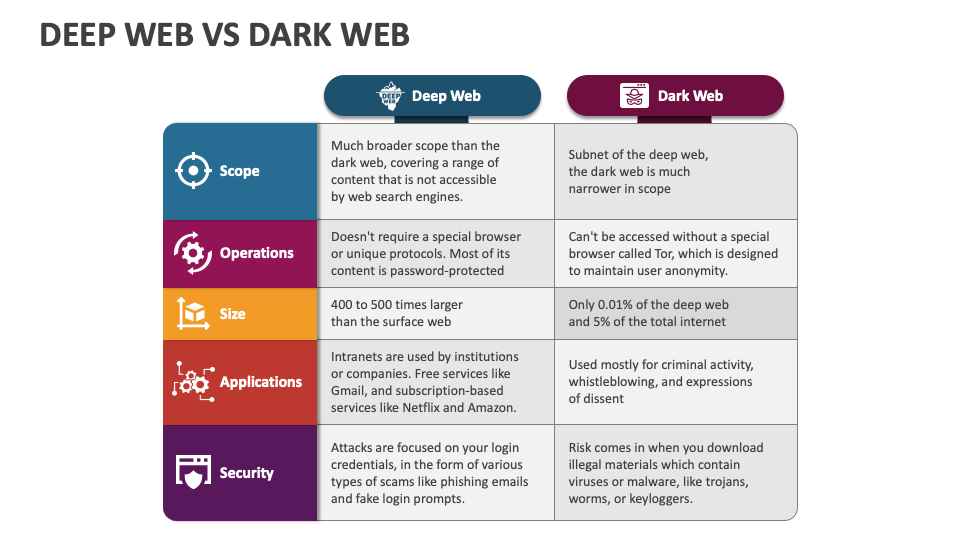
Lately, hackers have been in the news due to attempts to sell stolen data on the dark web. Most of us interact with the Deep Web daily—every time we log into email or work on a company intranet. Despite its “hidden” nature, the Deep Web is essential for preserving data confidentiality and ensuring that private information remains secure. It’s a critical component of the internet’s infrastructure, distinct from the often-overhyped realm of the Dark Web, which occupies just a small corner of this far larger digital expanse.
What Should I Do If My Social Security Number Is On The Dark Web?
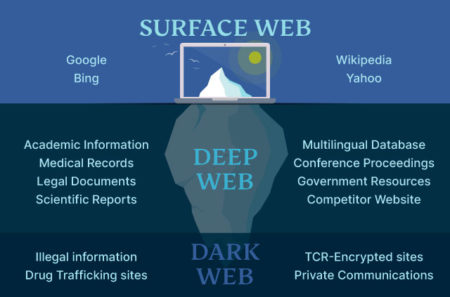
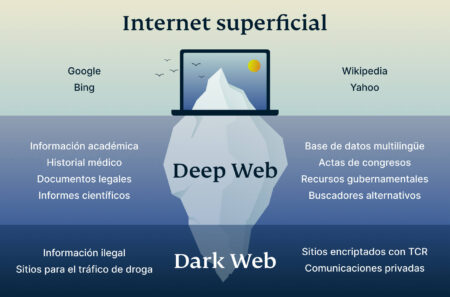
If the surface web is the visible part of an iceberg above water, the deep web is the part submerged beneath – much larger but hidden from plain view. Some people use the terms ‘dark web’ and ‘deep web’ interchangeably; however, significant portions of the deep web are completely legal and safe to use. This is akin to the things you actively hide from other people and don’t want anyone else to learn about. They don’t have to be deep, dark secrets — not even your closest friends need to know the password to your email account, for instance. The dark web is a part of the deep web, but only a very tiny part of it.
Cybercriminals, internet scammers, hackers, and internet brokers use it for lethal purposes. People use the Dark web for purposes of Human trafficking, hiring hitmen, selling weapons and drugs, child pornography, racist content, and content that speaks hate about minorities and otherwise. One cannot reach the Dark Web so easily since they have created strong encryption that is unreachable to the average user. The risks of accessing the deep web vs. the dark web may be similar but not exactly the same. Think about how many people will see the Gmail login screen on the clear net and how many individual Gmail accounts there are on the deep web. Now apply that logic to everything else, and you can start to grasp the difference in scale.
It is not accessible by your day-to-day web browsers but something can be hideous in nature if you are unaware of the conditions. The deep web can include secrets that get accidentally leaked, such as sensitive data from GitHub repos and paste sites. In addition, messaging platforms such as Telegram can be a complement to dark web forums and marketplaces. They offer a place for threat actors to connect and discuss tactics, sell stealer logs, and more.
Dark Web Vs Deep Web Monitoring: What Security Teams Need To Know
The dark web is a hidden part of the internet where illicit activities thrive and anonymity is prioritized. As such, it is a breeding ground for various types of threats that can jeopardize both individuals and organisations. From cybercriminals and hackers to illegal marketplaces and scams, the dark web poses a wide range of dangers that users must be aware of in order to protect themselves and their sensitive information. Understanding the types of threats on the dark web is crucial for taking the necessary precautions to safeguard against potential harm. The dark web plays a critical role in cybersecurity because it serves as a hidden marketplace and communication hub for cybercriminals. This anonymous layer of the internet enables the sale and exchange of stolen data, such as login credentials, credit card numbers, intellectual property, and sensitive corporate information.
Potential Risks
Once you have it, keep your identity and devices protected with Frontier’s security support. The deep web is a subset of the web containing websites that cannot be located by search engines. Anything that does not show up on Google can be found on the deep web. Search engines crawl the internet through links, visiting one web page, the links on that page and so on, keeping track of all the information. What cannot be accessed by search engines is referred to as part of the deep web. Before we understand what the dark web is, let’s take a look back at our trusty World Wide Web.
Dark Web Reveals Tech Companies Leak Most User Data
Since the internet is not safe, using a Tor browser can protect the user’s system and virtual activities from the prying eyes of the ISPs and third-party internet criminals. It masks all of the user’s internet browsing to have complete security and anonymity to access any site without the fear of leaving the digital footprints. The anonymous part of the internet and Deep Web segment that conventional Google search engines cannot optimize is called the Dark Web.
Onion Routing
- It includes content that is behind paywalls, private databases, and other unindexed sites.
- Now, let’s explore their differences in more detail, how to access them, and dispel some misconceptions along the way.
- Just because a page cannot be accessed by search engines doesn’t mean it’s trying to promote illicit activity.
- This includes social media, news sites, blogs, and e-commerce sites accessible to most users with minimal effort to find and access them, without special software or login credentials.
- Like other parts of the internet, the dark web has scams and third parties trying to steal your data through phishing.
- However, the dark web’s anonymity makes it a breeding ground for criminal activities.
And within that ocean, the protected dark web provides a secure refuge for illegal activities. Universities and medical providers need to keep confidential content out of the public eye. Website owners often use the robots.txt file to manage traffic and determine what data search engines can access.
While it protects your identity, it can also expose you to interactions with dangerous threat actors. The Deep Web refers to parts of the internet that aren’t indexed by standard search. Scammers often target users on the dark web, employing phishing tactics to steal personal information and financial details. These scams can result in significant financial loss and identity theft.
Are Sites On The Dark Web Illegal To Use And Visit?
Security teams often focus on dark web monitoring while overlooking equally critical deep web sources like GitHub or Telegram. However, threats can often originate in the deep web before escalating to the dark web. Falling for these scams can result in financial loss, identity theft, and even physical harm.
Unlike the deep web, the dark web is intentionally hidden and requires specialized software like The Onion Router (TOR) to access it. This ensures a high level of anonymity and privacy by encrypting users’ data and bouncing their internet traffic through a series of servers around the world. The dark web itself is not inherently illegal to use or visit, as it is simply a part of the internet that is not indexed by traditional search engines and requires specific software to access. However, the dark web is notorious for hosting illegal activities, such as drug trafficking, weapons sales, counterfeit money, and various forms of illegal pornography. On the other hand, the deep web refers to the vast portion of the internet that is not indexed by search engines. This includes confidential databases, academic journals, private social media content, and other information that is not easily accessible to the public.
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Moreover, the anonymity that protects users can also be a double-edged sword. It comprises just a tiny fraction of the Deep Web, but its potential for misuse makes it a subject of significant concern for security teams and law enforcement. In stark contrast, the Dark Web can only be accessed using specialized software like the Tor browser. These aren’t hidden for nefarious reasons, but rather to protect sensitive or personal information.
Get The Latest Insights, Trends And Security News Subscribe To CyberheistNews
While the deep web is definitely safer than the dark web and its criminal activities, some unindexed sites may contain the same threats. In fact, since the deep web can be accessed from a regular browser, you actually have to be more careful. When most people talk about the deep web, the conversation often turns to nefarious or malicious uses.

There are many clear, deep, and dark web sites, forums and marketplaces where threat actors can access victims’ online accounts. In addition, encrypted messaging platforms like Telegram and QQ provide a safe haven for communications about malicious acts and are, therefore, popular among threat actors. The deep web is any part of the internet that is not indexed by search engines, and it accounts for roughly 90% of all the internet’s content.
That’s why privacy-focused users often combine Tor with end-to-end encryption tools like PGP or services like Mailfence, which support secure, encrypted communication even outside of hidden networks. It is essential to understand the potential risks of being monitored by law officials, as they may gather evidence that could lead to legal repercussions. It can help identify any potential threats and alert you to any signs of monitoring or compromise. To protect yourself from government monitoring on the dark web, it is crucial to take certain precautions. Firstly, use a reliable VPN to hide your IP address and avoid being tracked by law enforcement.



