Check around with other users and ask if they know anything about the new marketplace. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains.
While not mandatory, using a VPN adds an extra layer of privacy and security by hiding Tor usage from your internet service provider. These websites will now work without issues, as the VPN hides the exit node and makes your traffic look inconspicuous. In practice, we found very little use of VPN Over Tor and saw no significant advantages.
Empower Your M&A Activity With Open Source Intelligence (OSINT) Techniques
They engage in financial crime and sell other people’s stolen personal information, since they’re under the veil of anonymity. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities. Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky. These hackers don’t hide in the shadows as much as you might think.

Stay Safe
While you can visit the obscure part of the internet without a VPN, it’s better to go with one. Here are our favorite choices that work well and support Tor Over VPN perfectly. This method is far more complex but we’ll still explain it for those too curious. As opposed to the previous situation, here, you’re first connecting to Tor and then the VPN. Not many providers support this, so a manual and sometimes tedious configuration is needed. The exit node can also be compromised but our experience has shown this happens extremely rarely.
What Is A Cloud Access Security Broker?
When engaging in online activities over Tor, refrain from providing identifying information, including your name, email address, or financial details. Create new handles or pseudonyms to protect your identity throughout your online engagements. Here are some of the popular ones, exclusively hosted in the darknet. Web search in late 90x, total fun – that required luck and skill. Search algorithms back then used to be based on exact words matching and presented based on resource popularity and number of cross-references. Btw today’s search engine provides you with information that the algorithm considers being your intend (adjusted to probability), and there is far more complexity involved.
Search Code, Repositories, Users, Issues, Pull Requests
Accessing the dark web is legal in India as long as you do not engage in illegal activities such as buying drugs or hacking services. During this process, your ISP can still see that you’re using Tor because the entry node is now fully visible. Not to mention the entry node will see your IP address, so if it’s compromised, a hacker would be able to get a hold of it. More importantly, even the VPN service will now see what you’re doing inside Tor. It encrypts your traffic right away, which is beneficial if you don’t want your ISP to see you’re using Tor.
It is important to verify that the application is indeed published by “The Tor Project, Inc.” to avoid installing potentially malicious imitations. These endorsed apps have been reviewed by the Tor Project and are considered trustworthy options for routing iOS traffic through the Tor network. If you want to access the dark web, your first step toward a more private experience should be to secure your internet connection and data with a reliable VPN. Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online.
FAQ: More About Onion Sites
Swiss based e-mail service, encrypts e-mails locally on your browser. mark it means it has been verified as a scam service and it should be avoided. If the website you are trying to visit has Recommended mark it means it has been verified and is safe to use.|The Tor Browser prevents your ISP from seeing what websites you’re visiting, but it does not prevent the ISP from seeing that you’re using Tor. As I mentioned previously, using the Tor Browser will slow down your browsing. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting).|However, if we’re being honest, the majority of activity on darknet markets involves illegal or heavily regulated items. A 2020 study found that almost 57% of sites on the Tor network hosted some form of illegal content. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more.|But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. Since you’ve now installed the Tor browser, you can safely browse dark web websites and other (previously) hidden websites.}

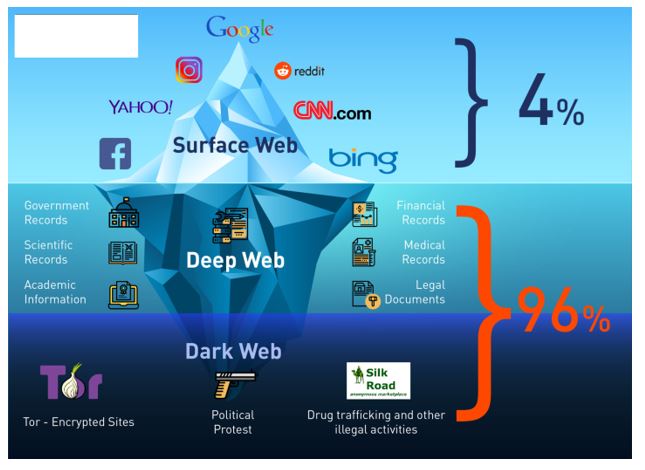
You’re only scratching the surface when you use the Internet for daily activities—reading news, managing finances, running businesses. Search engines like Google, Bing, and Yahoo can access just about 4% of the web. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe.
What Is WPA2 (Wireless Protected Access ?
Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. Due to its absolute anonymity for knowledgeable users, the chance of running into bad people is also realistic, as they can operate relatively freely without the fear of getting caught doing something unlawful. However, if you must buy items from the dark web, set up a secure, encrypted email with CounterMail or ProtonMail. For more information, read more about the most secure email service providers in my other post. The majority of the users on the dark web use the Tor (The Onion Router) browser.
Navigating Ransomware Attacks While Proactively Managing Cyber Risks

ZeroBin offers an extra secure version of this service by only encrypting and decrypting text in the browser, meaning their servers have no knowledge of what is passing through it. Onion sites (aka Tor sites) are websites only accessible on the dark web; you can’t view them using a regular browser. Their URLs (aka dark web links) have .onion as the domain, instead of the common surface web domains like .com or .net. Viewed from the destination, the traffic appears to originate at the Tor exit node. The dark web is web content that exists on darknets, which are overlay networks on the internet that require specialized software (such as the Tor Browser), configurations, and authorization to access.
It’s not illegal per se to access an onion website, but that doesn’t mean your actions while connected to the dark web are immune from law enforcement. It’s still illegal to commit crimes while connected to Tor, regardless of whether or not you think you’ll be caught. Ahmia is a dark web search engine designed to index and search tor websites.
- With all of those settings combined, you can be sure that the Tor Browser minimizes any vulnerabilities you could have and blocks any malware, phishing attempts, or other cyber threats.
- VPNs, proxies, and alternative privacy-focused networks like I2P and Freenet also offer unique advantages.
- Keep in mind that while Tor anonymizes your browsing activity, it is not foolproof.
- Thankfully, with the right guide — and a tool like a VPN (Virtual Private Network) by your side — you can navigate these hidden sites safely without falling victim to any hazards along the way.
- You can access these websites without worrying about someone snooping on a Tor exit node, offering more private browsing of what is known as the deep web.
- Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky.
While Tor offers strong privacy protections, it comes with notable drawbacks that can make it impractical for everyday use, and the dark web content it grants access to can put users at risk. By using a VPN to connect to Tor — a special browser designed to access the dark web — you can securely access the dark web using a technique known as Tor-over-VPN. Without a VPN, your ISP or network administrator may be able to detect, monitor, or block dark web access; Tor-over-VPN provides an extra layer of privacy. However, there are plenty of legal and legitimate online activities that require privacy and anonymity. The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web.